
CMMC for IT Professionals: An Implementation Guide for Compliance
If you’re an IT professional looking to increase your knowledge in cybersecurity, understanding how to implement the Cybersecurity Maturity Model Certification (CMMC) is essential. Preparation for CMMC can seem daunting, but with the proper strategies and guidelines, it comes within reach. This page aims to demystify CMMC in IT, providing you with an impactful implementation guide for compliance. Here, we’ll break down the CMMC implementation steps to assist your organization in meeting necessary security mandates and raising your cybersecurity maturity.
In this blog post, we’ll provide a comprehensive overview of CMMC and what compliance means for IT professionals. We’ll address key requirements and provide sound recommendations to assist IT professionals in preparing for and maintaining CMMC compliance.
The CMMC certification process is arduous but our CMMC 2.0 compliance roadmap can help.
CMMC Overview
The Cybersecurity Maturity Model Certification (CMMC) is a unified cybersecurity standard that the U.S. Department of Defense (DoD) designed to safeguard sensitive federal contract information and unclassified defense information within the defense supply chain, or defense industrial base (DIB). The CMMC 2.0 framework comprises three maturity levels that range from basic cybersecurity hygiene to highly advanced practices. The primary essence of CMMC is to ascertain that defense contractors have the appropriate cybersecurity controls in place to protect sensitive data.
It’s important to comprehend the pivotal role CMMC plays in the defense sector. It ensures the necessary security measures are in place to protect the integrity of federal contract information (FCI) and controlled unclassified information (CUI). By providing a standard by which all defense contractors must abide, CMMC upholds the national security interests of the United States. Furthermore, a globally competitive defense industrial base that is secure from cyber threats is key to the U.S.’s strategic advantage.
The Importance of CMMC Compliance
Compliance with CMMC standards is not just a recommendation; it’s a requirement for contractors working with the DoD. Not achieving or maintaining this certification can have severe ramifications. Firstly, defense contractors risk losing their DoD contracts if they are not CMMC compliant. This can translate into significant financial losses and loss of business opportunities.
In addition to financial losses, defense contractors risk legal repercussions for non–compliance. They may face lawsuits, regulatory fines, or even criminal charges in cases of severe negligence or intentional misconduct. Beyond the financial and legal consequences, non–compliance can tarnish a company’s reputation, causing immeasurable damage that could take years to rebuild. Hence, achieving and maintaining CMMC certification is of paramount importance for defense contractors.
Preparing for CMMC Compliance
IT professionals tasked with preparing an organization for CMMC compliance will have their hands full. Their efforts will be scrutinized during a CMMC audit. The following recommendations should help, particularly as it pertains to handling, sharing, and storing CUI and FCI.
Identify Data to Be Shared With DoD
The first crucial phase that IT departments must undertake to ensure their organization adheres to the CMMC requirements is to pinpoint the nature of data being utilized in their DoD contracts.
This critical step involves thoroughly analyzing and categorizing the data to understand its sensitivity level and consequently, which CMMC controls should be applied to ensure its protection. The type of data used within the DoD contracts will directly inform the methods used for safeguarding it. This assessment will guide the IT department in implementing the necessary controls and security measures required by the CMMC Level 2. This level is primarily targeted towards establishing and meticulously documenting the practices and policies that will steer the implementation of the Controlled Unclassified Information (CUI) protection capacity within the organization.
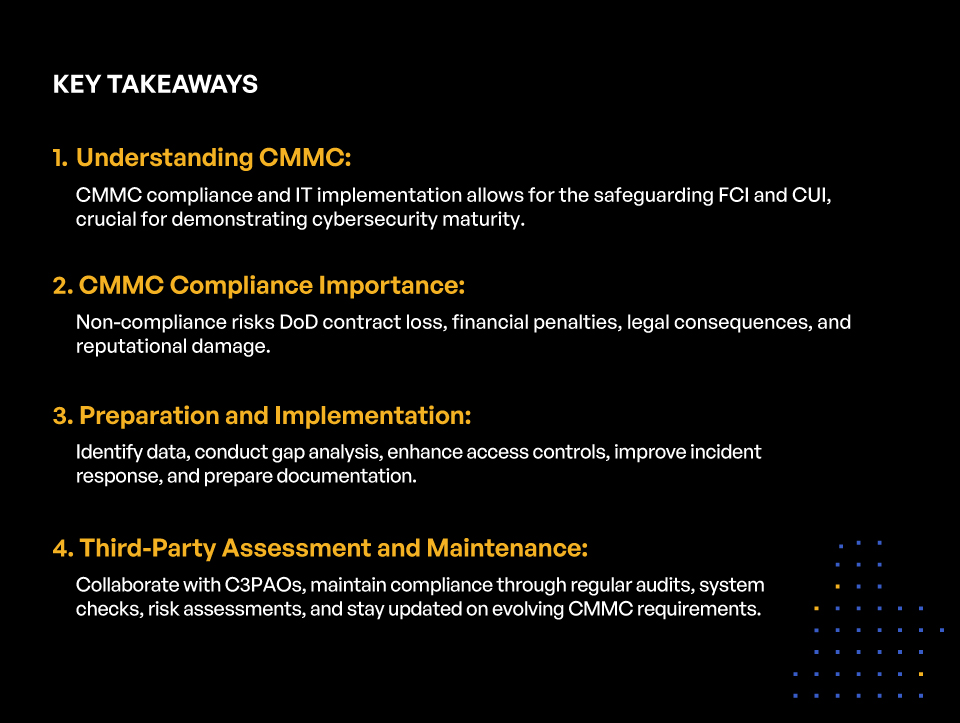
KEY TAKEAWAYS
- Understanding CMMC:
CMMC compliance and IT implementation allows for the safeguarding FCI and CUI, crucial for demonstrating cybersecurity maturity. - CMMC Compliance Importance:
Non-compliance risks DoD contract loss, financial penalties, legal consequences, and reputational damage. - Preparation and Implementation:
Identify data, conduct gap analysis, enhance access controls, improve incident response, and prepare documentation. - Third-Party Assessment and Maintenance:
Collaborate with C3PAOs, maintain compliance through regular audits, system checks, risk assessments, and stay updated on evolving CMMC requirements.
The CMMC Level 2 also necessitates creating and implementing a detailed system security plan (system security plan). This plan should outline the various practices and strategies that will be adopted to execute these policies effectively. The intent is to foster a more mature and progressive cybersecurity posture, aligning with the CMMC’s objective of protecting the federal contract information and CUI within the DIB. The SSP should not merely be a static document, but rather a practical, actionable roadmap that provides clear directions on how the organization should handle and protect CUI. It should entail risk management strategies, incident response plans, regular audits, and compliance checks, amongst other critical elements.
Conduct a Gap Analysis
Implementing CMMC requires IT professionals to also identify potential gaps in their organization’s existing security controls. This is a critical step that provides a clear picture of the organization’s current security posture and areas that need improvements. Understanding and identifying these gaps help in ensuring compliance and protecting sensitive defense information.
A thorough review of the current security policies, procedures, and controls is the starting point. IT professionals need to assess the effectiveness of the existing incident response mechanisms, personnel training, data access controls, and network security measures. Identifying weaknesses in these areas is essential in determining how an organization measures up to the CMMC’s set standards.
Another crucial factor to consider is how well the organization manages CUI. As part of the CMMC certification, IT professionals must ensure that there are sufficient procedures to protect CUI at all levels of the organization. Any gaps in the protection of CUI can lead to compliance issues, making this a priority during the gap identification process.
Finally, the use of the CMMC’s maturity processes and cybersecurity practices provides a benchmark for identifying gaps. By comparing the organization’s current security controls with these standards, IT professionals can easily spot areas that need improvement. It is only by thoroughly identifying and understanding these gaps that an effective plan for CMMC compliance can be developed.
In total, identifying gaps in the existing security controls is a complex task that requires a comprehensive understanding of the organization’s security infrastructure and the CMMC’s requirements. This process is crucial to achieving successful CMMC certification and ensuring robust cybersecurity practices in the organization.
Implement Necessary Changes
The next step after identifying the gaps in the existing security controls is implementing the necessary changes. This step could involve a range of activities, such as conducting staff trainings, enhancing the current access control measures, and improving incident response procedures. These changes should aim to meet the 110 practices across the 14 domains as required by CMMC Level 2. We’ll take a closer look at each below.
Conduct Staff Trainings
Another crucial aspect to consider during the implementation phase is security awareness training. Employees need to understand the new changes, why they are necessary, and how to properly execute them. Training programs should be designed to provide employees with the necessary knowledge and skills to support the company’s cybersecurity efforts. A well–crafted training program can significantly enhance a company’s cybersecurity by ensuring all employees understand their roles and responsibilities in protecting sensitive information.
Furthermore, regular training sessions can help to keep staff updated on the latest data security practices and understand the specific roles they play in maintaining overall systems security. The CMMC certification process mandates a certain level of staff competence in cybersecurity. This not only helps to protect the organization’s data but also builds a strong culture of data security within the organization.
Lastly, staff training should also encompass the steps to take in the event of a security incident. By learning to respond swiftly and appropriately, the impact of any potential data breaches can be significantly reduced. These trainings ensure the organization is prepared for any eventuality, thereby cementing its commitment to maintaining a high level of cybersecurity as required by the CMMC.
Enhance Present Access Control Measures
As an IT professional, enhancing the existing access control measures is a crucial process within the CMMC framework. This initiative facilitates the protection of FCI and CUI from unauthorized access. The need to improve these measures stems from the rising cyber threats that put sensitive information at risk.
The process begins by understanding the current access control measures in place; this involves identifying who has access to what information and how that access has been granted. Subsequently, the gaps in the existing control measures can be identified, which could include issues such as shared usernames and passwords, unrestricted access to sensitive information, or lack of thorough audit trails for the access of confidential data.
Once gaps are identified, the next step is to implement enhancements. This could be in the form of multi–factor authentication (MFA), setting up strong access controls based on roles and responsibilities, and ensuring encryption and secure communication protocols. Also, monitoring, logging, and auditing access to sensitive data is crucial to mitigating potential threats or vulnerabilities. Each measure is geared towards meeting the access control requirements stipulated in the CMMC model.
Regular review of access control measures is another crucial aspect. The security landscape is dynamic and evolves with time; therefore, it is vital to keep abreast with changes and update control measures periodically. This allows for timely identification of potential weaknesses and implementation of necessary mitigation strategies.
Improve Incident Response Procedures
One of the key aspects of the CMMC certification process is improving incident response procedures. An incident response plan ensures that organizations can react quickly and efficiently to any cybersecurity incident. Improving incident response procedures involves several key steps.
The first step is conducting a thorough risk analysis, which involves identifying potential threats and vulnerabilities in systems, networks, or data. Following the identification of threats, an appropriate mitigation strategy should be laid out.
Another essential part of the improvement process is conducting regular training and awareness workshops. These help ensure that every member of the organization understands their role in the response procedure. Regular testing of the incident response procedures is also key to ensuring that they work effectively when needed.
Additionally, communication is an essential aspect of an efficient response procedure. It is important to have a clear communication plan in place, detailing who will be contacted, how they will be informed, and what information will be conveyed in the event of an incident.
Lastly, an effective incident response procedure should include a follow–up process. This is essential for analyzing the incident, identifying areas that need improvement, and mitigating the possibility of such incidents occurring in the future.
The CMMC Audit Process
The final step in the CMMC compliance journey is the audit process. Contractors have to go through an audit conducted by a C3PAO to verify their compliance with CMMC requirements. The audit evaluates if the implemented security controls and practices effectively protect CUI or FCI as stipulated by the CMMC level the contractor is seeking to attain.
The review process could seem daunting, but with a well–maintained and documented cybersecurity infrastructure, defense contractors are likely to navigate it successfully. After the audit, contractors receive their CMMC certificate, which is valid for three years. However, during this period, they must keep their cybersecurity practices up–to–date and consistent with the CMMC requirements.
Self–Assessment
Regular self–assessment allows IT professionals to evaluate their cybersecurity practices to ensure they meet the prescribed CMMC standards.
IT Professionals should conduct internal audits to identify any potential areas of concern or risk. This enables IT professionals to anticipate the issues that will be explored during the third–party assessment. Appropriate corrective measures can then be taken to resolve any existing problems or vulnerabilities.
Before undertaking a CMMC self–assessment, it’s imperative for IT professionals to have a clear understanding of the CMMC framework. This includes comprehending the various maturity levels and the requisite security controls at each level. Professionals should also understand how to map these controls to their organization’s IT infrastructure.
Even with a solid comprehension of the CMMC framework, success is dictated by the effectiveness of the implemented cybersecurity practices. So, it is important to implement, review, and refine existing practices following the guidance of the CMMC model. This continuous improvement process fosters the resilience and robustness of an organization’s cybersecurity posture.
In preparation for the self–assessment, IT professionals should perform a comprehensive evaluation of their existing cybersecurity infrastructure. This includes checking the performance of firewalls, intrusion detection systems, data encryption, password protection, and other security measures. It’s important to identify and address any vulnerabilities as these can lead to severe breaches.
Finally, engaging in awareness and training programs is a key part of being prepared for a CMMC self–assessment. These initiatives assure that all personnel involved understands their roles and responsibilities concerning the organization’s cybersecurity. As CMMC is a fairly new model, it’s vital to remain updated on any changes to the certification requirements.
In conclusion, a successful CMMC self–assessment is a result of understanding the CMMC model, implementing effective cybersecurity practices, and ensuring continuous updates on the latest changes in the certification requirements.
Third–party Assessment
A crucial step in the CMMC certification process is the third–party assessment or audit, conducted by a certified third–party assessor organization (C3PAOs). IT professionals should be prepared for this extensive evaluation, which is critical to achieving certification.
Preparation for a CMMC assessment includes evaluation of current cybersecurity systems, identification of gaps, and implementation of controls to fill those gaps.
Assess the Scope of the CMMC
IT professionals must first understand the overall scope of the CMMC to ensure their approach is comprehensive. IT professionals can then identify the specific security controls and practices that need to be implemented according to the required maturity level in accordance to their organization’s needs for the protection of Controlled Unclassified Information (CUI).
Conduct an Internal Audit
Conducting an internal audit is a crucial step in implementing CMMC. The purpose of an internal audit is to provide a clear picture of the work needed to reach the desired CMMC level. This involves assessing the current state of an organization’s cybersecurity measures and identifying the gaps between the existing measures and the CMMC requirements.
Prepare Relevant Documentation
Documentation plays a key role in preparation for CMMC. It serves as proof of a system’s compliance with CMMC requirements. This includes policy documents, system security plans, and records of implementing practices. Thorough and accurate documentation not only supports compliance but also helps to streamline third–party assessments, making the review process efficient and ensuring no crucial details are overlooked.
Effectively Communicate with the C3PAO
It is critically important for IT professionals to actively engage in open communication and dynamic collaboration with the C3PAO. The relationship with the C3PAO should be viewed as an opportunity for growth and improvement, rather than just a means to pass the assessment.
A collaborative relationship with the C3PAO is beneficial to both parties involved. For the IT professionals, they can obtain guidance on the best cybersecurity practices and also get clear answers to any questions they may have. Additionally, the C3PAO can provide valuable insights into areas of cybersecurity that might not be up to the standard, which can then be rectified before the formal assessment.
By building a good relationship and maintaining open lines of communication with the C3PAO, IT professionals can ensure a more seamless and effective assessment process.
Maintaining CMMC Compliance
Once the necessary changes have been made, the next step is to maintain CMMC compliance. This necessitates regular monitoring and review of security measures to ensure they continue to meet the CMMC standards. IT departments should conduct random audits, consistent system checks, and perform risk and vulnerability assessments to ensure the security measures remain effective against evolving cyber threats.
Moreover, as CMMC requirements can change over time, IT departments should regularly review these requirements. This would ensure their systems, processes, and policies stay up–to–date with the latest regulations. Remember, maintaining CMMC compliance is an ongoing process, not a one–time task. It involves continuous effort and commitment to security and risk management.
Role of IT Departments
A critical role played by IT departments within the context of maintaining CMMC compliance involves conducting unscheduled and random audits. These audits provide a comprehensive examination of the existing cybersecurity measures, ensuring they meet the required standards. The audits help identify any potential lapses in security measures that could potentially facilitate unauthorized access or data breaches.
Moreover, IT departments are also responsible for executing consistent system checks. These checks are essential to verify the operational integrity and efficiency of system defenses. Regular system checks allow for the timely identification and rectification of any software bugs, security vulnerabilities, or system failures that could compromise data security.
Another fundamental duty of IT departments in maintaining CMMC compliance is performing risk and vulnerability assessments on a regular basis. These assessments help in identifying the susceptibility of the system to various potential threats and evaluating the devastating impact that these threats could inflict if not properly mitigated. By identifying these vulnerabilities, organizations can take proactive measures to strengthen their systems and mitigate possible risks.
Review CMMC Requirements
CMMC requirements are not static; they can evolve over time, reflecting changes in cybersecurity threats and technology advancements. As such, it becomes critically important for IT departments within organizations to stay abreast of these adjustments.
IT departments should schedule regular reviews of these CMMC requirements. In these review sessions, they should compare the current regulations with their existing cybersecurity measures and identify any areas of misalignment.
Where differences are spotted, IT management should then plan and implement the necessary adjustments to their systems, protocols, or procedures. These modifications could take the form of software updates, hardware upgrades, or even changes in cybersecurity policies and user training. By ensuring that they remain on top of these updates, organizations and IT departments can maintain their compliance with CMMC regulations. Doing so not only safeguards the organization from potential cyber threats but also ensures it does not attract penalties for non–compliance.
Furthermore, adhering to the most recent regulations guarantees that systems and processes are not only safe but also efficient and competitive, given that these regulations are often based on industry best practices.
Perpetually Prepare for CMMC Audits
Regular auditing stands as a vital part of maintaining CMMC compliance, ensuring adherence to the set of standards aimed at protecting sensitive federal information stored on contractors’ systems.
Conducting audits regularly helps organizations ensure their ongoing adherence to the policies, procedures, and guidelines set forth by the CMMC. These comprehensive audits involve a detailed examination of the existing computer systems and IT infrastructure. By conducting such in–depth scrutiny, it becomes possible to inspect if all cybersecurity measures are adequately implemented, assess the level of system security, and ensure that the organization meets the desired level of cyber hygiene and CMMC maturity level.
Audits also play a crucial role in identifying any potential shortcomings or vulnerabilities in the system that may be exploited by cybercriminals. These could include unpatched software, weak passwords, outdated hardware and software, or a lack of employee awareness about phishing attacks and other cybersecurity threats. Once these weaknesses are identified, they can be promptly addressed and rectified to reinforce the organization’s cyber defenses.
Kiteworks Helps IT Professionals Prepare for and Maintain CMMC Compliance with a Private Content Network
In conclusion, CMMC plays an essential role in protecting sensitive defense information within the defense industrial supply chain. Adherence to these standards is critical, as non-compliance can lead to significant financial, legal, and reputational damages. Therefore, IT departments play a pivotal role in implementing and maintaining cybersecurity measures that comply with CMMC standards.
Implementing a CMMC–compliant secure file sharing solution involves identifying the type of data used in DoD contracts, conducting a gap analysis, making necessary changes, and training the staff. Maintaining compliance requires regular monitoring and review of security measures, and staying updated with CMMC requirements. Finally, the journey culminates in a thorough audit process to verify compliance.
As cybersecurity threats continue to evolve, the demand for CMMC compliance will only increase. Therefore, IT professionals must equip themselves with the necessary knowledge and skills to navigate this landscape successfully. Remember, achieving and maintaining CMMC compliance does not only safeguard national security but also presents an opportunity for defense contractors to differentiate themselves in an increasingly competitive market.
The Kiteworks Private Content Network, FIPS 140-2 Level validated secure file sharing and file transfer platform, consolidates email, file sharing, web forms, SFTP and managed file transfer, so organizations control, protect, and track every file as it enters and exits the organization.
Kiteworks supports nearly 90% of CMMC 2.0 Level 2 requirements out of the box. As a result, DoD contractors and subcontractors can accelerate their CMMC 2.0 Level 2 accreditation process by ensuring they have the right sensitive content communications platform in place.
With Kiteworks, DoD contractors and subcontractors unify their sensitive content communications into a dedicated Private Content Network, leveraging automated policy controls and tracking and cybersecurity protocols that align with CMMC 2.0 practices.
Kiteworks enables rapid CMMC 2.0 compliance with core capabilities and features including:
- Certification with key U.S. government compliance standards and requirements, including SSAE-16/SOC 2, NIST SP 800-171, and NIST SP 800-172
- FIPS 140-2 Level 1 validation
- FedRAMP Authorized for Moderate Impact Level CUI
- AES 256-bit encryption for data at rest, TLS 1.2 for data in transit, and sole encryption key ownership
Kiteworks deployment options include on-premises, hosted, private, hybrid, and FedRAMP virtual private cloud. With Kiteworks: control access to sensitive content; protect it when it’s shared externally using automated end-to-end encryption, multi-factor authentication, and security infrastructure integrations; see, track, and report all file activity, namely who sends what to whom, when, and how. Finally demonstrate compliance with regulations and standards like GDPR, HIPAA, CMMC, Cyber Essentials Plus, IRAP, and many more.
To learn more about Kiteworks, schedule a custom demo today.
Additional Resources
- Blog Post Choosing Which CMMC Level Is Right for Your Business
- Video Join the Kiteworks Discord Server and Connect With Like-minded Professionals for CMMC 2.0 Compliance Support
- Blog Post A Roadmap for CMMC 2.0 Compliance for DoD Contractors
- Guide CMMC 2.0 Compliance Mapping for Sensitive Content Communications
- Blog Post 12 Things Defense Industrial Base Suppliers Need to Know When Preparing for CMMC 2.0 Compliance