Secure Email for Client Communication
Legal professionals often need to communicate sensitive information via email. Traditional email can be insecure and lead to data breaches. Kiteworks provides secure email communication, ensuring that all communication is encrypted and only accessible to the intended recipient.
Secure File Sharing for Case Files
Legal professionals often need to share sensitive case files with clients, opposing counsel, or other stakeholders. Insecure file sharing can lead to data breaches. Kiteworks provides a secure file sharing platform that allows legal professionals to share sensitive case files securely, ensuring data integrity and confidentiality.

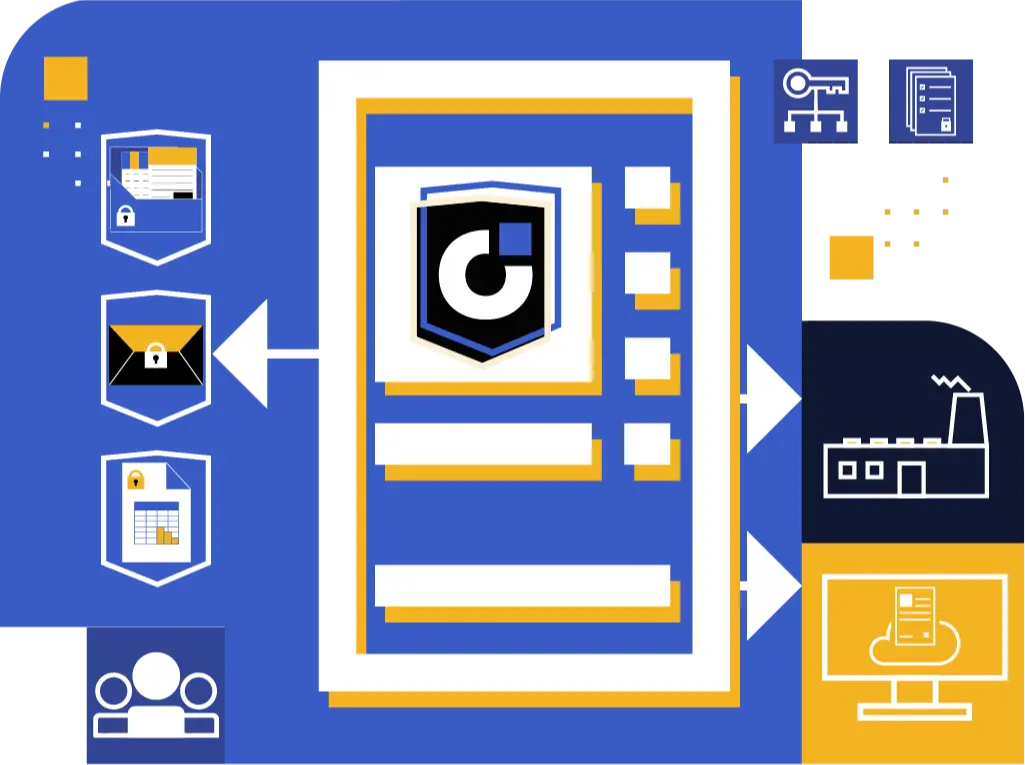
Managed File Transfer for Legal Documents
Legal departments often need to transfer large volumes of legal documents between systems or to external partners. Insecure file transfers can lead to data breaches. Kiteworks provides a managed file transfer solution that enables legal departments to securely transfer large volumes of legal documents, ensuring data integrity and confidentiality.
Secure Web Forms for Client Intake
Legal departments often need to collect sensitive information from clients during the intake process. Traditional web forms can be insecure and lead to data breaches. Kiteworks provides secure web forms that ensure personally identifiable information (PII) protection. The platform’s encryption and secure data storage capabilities ensure that client data is collected securely and stored safely.


Secure Email for Court Notices
Legal departments need to securely send and receive court notices. Traditional email can be insecure and lead to data breaches. Kiteworks provides secure email communication, ensuring that court notices are encrypted and only accessible to the intended recipient.
Secure File Sharing for Legal Research
Legal professionals often need to share sensitive legal research with colleagues or clients. Insecure file sharing can lead to data breaches. Kiteworks provides a secure file sharing platform that allows legal professionals to share sensitive legal research securely, ensuring data integrity and confidentiality.

Managed File Transfer for Discovery Documents
During the discovery process, legal departments often need to transfer large volumes of documents. Insecure file transfers can lead to data breaches. Kiteworks provides a managed file transfer solution that enables legal departments to securely transfer large volumes of discovery documents, ensuring data integrity and confidentiality.
Secure Web Forms for Legal Services Requests
Legal departments often need to collect sensitive information from clients when they request legal services. Traditional web forms can be insecure and lead to data breaches. Kiteworks provides secure web forms that ensure personal information protection. The platform’s encryption and secure data storage capabilities ensure that client data is collected securely and stored safely.

Secure Email for Legal Advice
Legal professionals often need to communicate sensitive information via email. Traditional email can be insecure and lead to data breaches. Kiteworks provides secure email communication, ensuring that all communication is encrypted and only accessible to the intended recipient.
Secure File Sharing for Contracts
Legal professionals often need to share sensitive contracts with clients, opposing counsel, or other stakeholders. Insecure file sharing can lead to data breaches. Kiteworks provides a secure file sharing platform that allows legal professionals to share sensitive contracts securely, ensuring data integrity and confidentiality.


Managed File Transfer for Legal Records
Legal departments often need to transfer large volumes of legal documents between systems or to external partners. Insecure file transfers can lead to data breaches. Kiteworks provides a managed file transfer solution that enables legal departments to securely transfer large volumes of legal documents, ensuring data integrity and confidentiality.
Secure Web Forms for Legal Document Requests
Legal departments often need to collect sensitive information from clients when they request legal documents. Traditional web forms can be insecure and lead to data breaches. Kiteworks provides secure web forms that ensure personal information protection. The platform’s encryption and secure data storage capabilities ensure that client data is collected securely and stored safely.

Secure Email for Confidential Correspondence
Legal professionals often need to send confidential correspondence via email. Traditional email can be insecure and lead to data breaches. Kiteworks provides secure email communication, ensuring that all confidential correspondence is encrypted and only accessible to the intended recipient.
Secure File Sharing for Legal Opinions
Legal professionals often need to share sensitive legal opinions with clients, opposing counsel, or other stakeholders. Insecure file sharing can lead to data breaches. Kiteworks provides a secure file sharing platform that allows legal professionals to share sensitive legal opinions securely, ensuring data integrity and confidentiality.
Managed File Transfer for Case Management Systems
Legal departments often need to transfer large volumes of data between case management systems or external partners. Insecure file transfers can lead to data breaches. Kiteworks provides a managed file transfer solution that enables legal departments to securely transfer large volumes of data between case management systems, ensuring data integrity and confidentiality.
Legal Solution FAQs
Kiteworks enables law firms to share sensitive case files securely with clients, opposing counsel, and court staff. Part of the Kiteworks Private Data Network, Kiteworks secure file sharing encrypts all communications in transit and at rest to maintain attorney-client confidentiality. Granular access controls let you specify exactly who can access specific documents, and possessionless editing lets you share a file without providing a download capability. Finally, all file activity—who sent what to whom—is tracked and recorded in comprehensive audit logs maintain chain of custody documentation and demonstrate regulatory compliance.
Kiteworks’ secure managed file transfer solution is specifically designed for handling large discovery document productions. Part of the Kiteworks Private Data Network, Kiteworks secure MFT securely transfers extensive document collections between systems or between users while maintaining data confidentiality, integrity and availability. The platform’s comprehensive tracking capabilities document all file access and transfers, providing the chain of custody evidence needed during discovery disputes and end-to-end encryption and granular access controls ensure these sensitive materials remain protected from unauthorized access.
Kiteworks secure web forms provide comprehensive protection for client intake processes. AES 256 encryption and a hardened virtual appliance deployed on a private, hybrid, or FedRAMP compliance authorized virtual private cloud ensures all personally identifiable and protected health information (PII/PHI) collected during intake remains protected. These secure forms can be embedded directly into your firm’s website or client portal, creating a streamlined yet fully protected onboarding experience that maintains client confidentiality from the very first interaction.
Kiteworks offers critical security advantages over Office 365 for legal communications. Unlike Office 365’s vulnerable RPMSG encryption, Kiteworks employs superior AES-256 encryption, TLS, S/MIME, and OpenPGP encryption. Additionally, Kiteworks email protection gateway ensures emails are protected with end-to-end encryption. While Microsoft can access your data with standard encryption keys when served with government subpoenas, Kiteworks does not have access to customers’ encryption keys and therefore no access to customer data. The platform provides delivery confirmation and comprehensive tracking capabilities that document when sensitive legal communications are received and opened. This creates a verifiable record of all legal correspondence while maintaining the confidentiality essential to attorney-client communications. Finally, Kiteworks supports file transfers up to 16TB versus Office 365’s 20MB limit, eliminating the risk of attorneys resorting to insecure workarounds when sharing large case files.
Kiteworks secure file sharing solution provides specialized capabilities for contract management workflows. As part of the Kiteworks Private Data Network, Kiteworks secure file sharing enables controlled document sharing with clients and opposing counsel with granular permission settings that determine who can view, edit, or share contracts. The solution’s comprehensive version control tracks all changes while comprehensive audit logs track and record all file activity, including uploads, downloads, shares, receipts, and more. This facilitates regulatory compliance, ensures data integrity throughout the negotiation process, and protects sensitive legal documents from unauthorized access.
FEATURED RESOURCES
Revolutionizing Legal Collaboration: Possessionless Editing
Optimize File Sharing Governance, Compliance, and Content Protection
2024 Kiteworks Sensitive Content Communications Security and Compliance Report
IT, SECURITY, PRIVACY, AND COMPLIANCE LEADERS AT THOUSANDS OF THE WORLD’S LEADING ENTERPRISES AND GOVERNMENT AGENCIES TRUST KITEWORKS