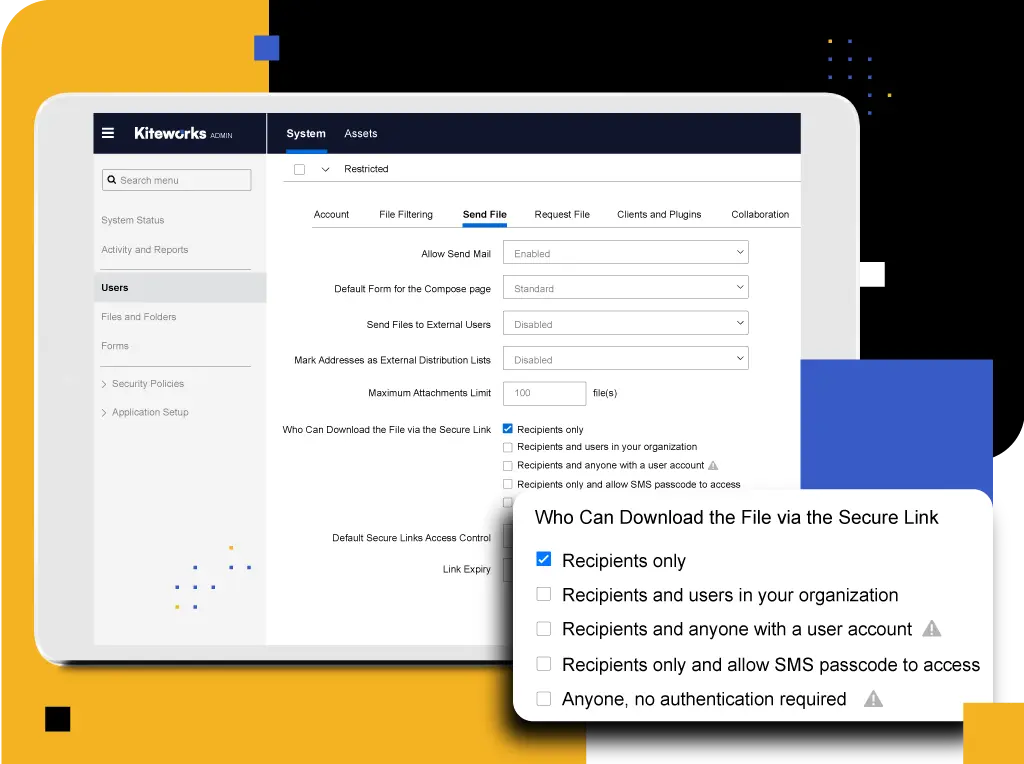
Enforce Compliance With Information System Security Policies
Standardise security policies across email, file sharing, mobile, MFT, SFTP, and more with the ability to apply granular policy controls to protect data privacy. Admins can define role-based permissions for external users, thereby enforcing NIS 2 compliance consistently across communication channels.
Support Business Continuity With Built-in Disaster Recovery
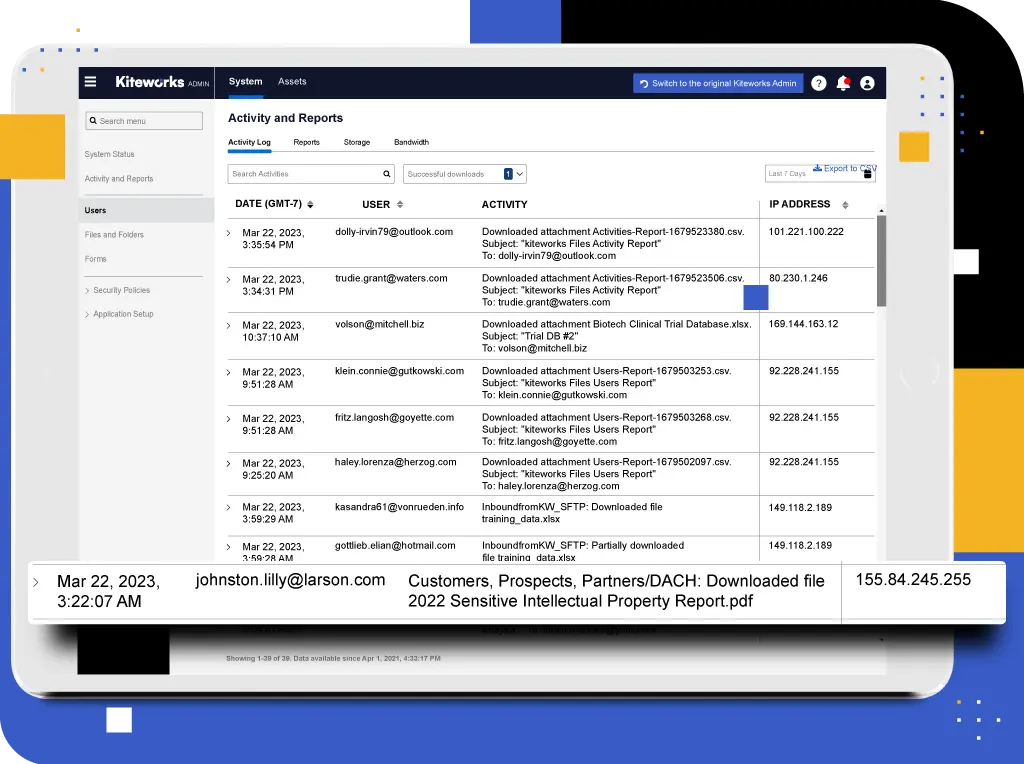
Maintain accurate records of all activities and technical data with user-friendly tracking displays, allowing audit logs to serve the dual purpose of ensuring that an organisation can investigate data breaches and provide evidence of compliance during audits. In the event of a breach, this grants an organisation the ability to see exactly what was exfiltrated so that they can get to work immediately on disaster recovery and continue their day-to-day business while maintaining compliance.
Manage Vulnerability in Development and Maintenance
Kiteworks enforces a strict secure software development life cycle, including extensive security code reviews, regular penetration testing, and a bounty program, to keep your data protected. Kiteworks also manages one-click updates for customers that have been tested for compatibility of the patch with other system components, allowing timely patches to the operating system, databases, and open-source libraries.

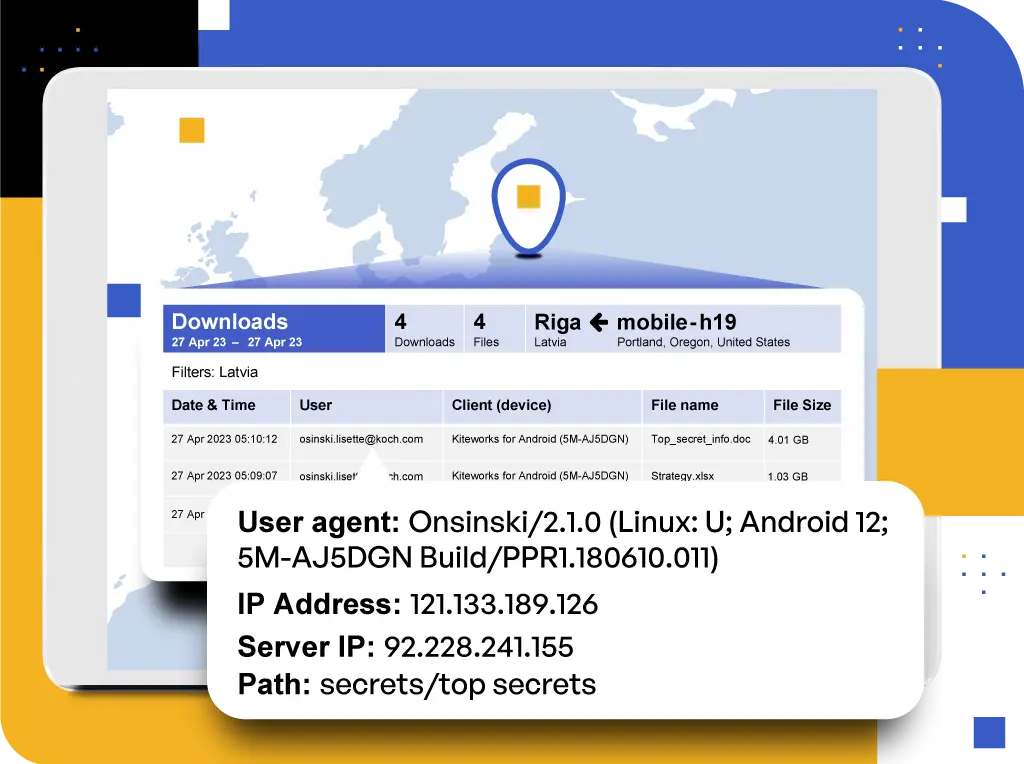
Handle Incidents With Efficiency
Anomaly detection allows for immediate insight into unauthorised access. Al technology detects suspicious events, such as possible exfiltration, and sends an alert via email and audit logs. Organisations can trust that attacks are detected sooner and maintain the correct chain of evidence to perform forensics, enabling efficient mandatory reporting of any data violations in a timely manner per the Directive.
Define and Enforce Basic Cyber Hygiene Practices
ISO has validated Kiteworks to effectively protect your sensitive data from cyber risk (ISO 27001), including when deployed as a cloud service (ISO 27017), and to shield your organisation from damaging leaks of personally identifiable information (PII) as validated by ISO 27018. Along with a library of other certifications, including SOC 2, plus single-tenant architecture and multilayered hardening, Kiteworks continues to validate its ability to mitigate data risk with the content management system and keep your basic cyber hygiene practices within NIS 2 compliance.


Protect Data With Encryption, Access Control Policies, and Multi-factor Authentication
The platform offers volume and file-level encryption of all data at rest with AES-256 encryption and TLS encryption in transit. The platform enables easy management of data, folders, invitations, and access controls. Access controls can be further managed within compliance with geofencing, app enablement, file type filtering, and email forwarding control. Apply granular multi-factor authentication and SSO policies by role and location utilising RADIUS, SAML 2.0, Kerberos, authenticator apps, PIV/CAC, SMS, and more. These features enable organisations to detect and respond to security incidents, manage vulnerabilities, and maintain compliance with NIS 2 requirements.
Frequently Asked Questions
The Network and Information Security (NIS) Directive is an EU-wide cybersecurity legislation that aims to achieve a high, common level of cybersecurity for essential services providers across the Member States. The proposed NIS 2 Directive rescinds the original NIS Directive and creates a more extensive and standardised set of cybersecurity requirements. NIS 2 encompasses some major changes, which include a wider scope of coverage, strengthened security requirements, increased collaboration, and faster incident reporting.
The NIS 2 Directive applies to any organisation with more than 50 employees whose annual turnover exceeds €10 million and any organisation previously included in the original NIS Directive. NIS 2 increases its scope to cover additional essential services, including electronic communications, digital services, space, waste management, food, critical product manufacturing (i.e., pharmaceuticals), postal services, and public administration.
Penalties for noncompliance with NIS 2 include fines of €10 million or 2% of the organisation’s total worldwide turnover—whichever of these numbers is higher. These fines mirror those imposed for GDPR violations. NIS 2 represents a significant leap in cybersecurity requirements and therefore should be treated as seriously as GDPR.
While NIS 2 will not apply to organisations in the UK directly, the UK government announced on November 20, 2022 that the UK’s Network and Information Security (NIS) regulations will be strengthened to allow for NIS 2 alignment in many areas to further protect essential services against digital threats like cyberattacks.
Under NIS 2, organisations must take appropriate and proportionate measures to manage the technical and operational risks to the network and information systems they rely on for operations or the provision of services. These measures include:
- Ensuring basic computer hygiene (cybersecurity) practices
- Implementing risk analysis and information system security policies
- Incident handling protocols
- Mandatory training for higher management
- Implementation of a disaster recovery plan
- Introducing supply chain and network security measures
- Encryption
- Strict use of multi-factor identity verification
- Secure communications
FEATURED RESOURCES
How to Achieve NIS 2 Compliance and Secure Your Content

NIS 2 Directive: Requirements, Obligations, and How Kiteworks Can Help With Compliance
Kiteworks Complies With ISO 27001, 27017, and 27018

Kiteworks and FCA Compliance Secure Customer Data and Streamline Operational Risk Management