
CMMC Compliance Guide for DIB Suppliers
Cybersecurity threats are becoming increasingly sophisticated and frequent, posing a significant risk to the Defense Industrial Base (DIB) and national security. To mitigate these risks, the Department of Defense (DoD) has implemented the Cybersecurity Maturity Model Certification (CMMC) framework, a comprehensive set of security standards that must be followed by all DIB suppliers.
CMMC 2.0 compliance is mandatory for all defense contractors, and failure to comply with the regulations can result in significant financial and reputational damage. In this post, we’ll walk you through CMMC 2.0 compliance for DIB suppliers. From assessing your current cybersecurity measures to successfully navigating a CMMC audit, we’ll help you understand how to implement the CMMC framework effectively. Finally, we’ll show you how Kiteworks simplifies the CMMC compliance process with our secure file transfer, email, and collaboration solutions.
The CMMC certification process is arduous but our CMMC 2.0 compliance roadmap can help.
What Is CMMC 2.0 Compliance?
CMMC 2.0 compliance is a set of cybersecurity standards that contractors must adhere to in the DIB. It is a unified standard for implementing cybersecurity across the entire DoD supply chain, from prime contractors to subcontractors. The CMMC framework is designed to provide a comprehensive, flexible, and scalable set of cybersecurity standards that can adapt to the evolving cybersecurity threat landscape.
The CMMC 2.0 framework builds on the previous version of CMMC and introduces changes to the compliance and certification process. At Levels 2 and 3, CMMC 2.0 certification requires assessment by a CMMC Third Party Assessor Organization (C3PAO), which ensures that contractors meet the necessary security requirements to protect controlled unclassified information (CUI) and other sensitive data.
Why CMMC Matters For Defense Industrial Base Suppliers
CMMC 2.0 compliance is mandatory for all defense contractors, regardless of their size or scope of work. Failure to comply with the regulations can result in the revocation of DoD contracts, financial penalties, and reputational damage. Compliance with CMMC 2.0 is essential for DoD suppliers to secure their place in the supply chain and maintain their competitiveness.
Moreover, CMMC 2.0 compliance is critical to national security. The DIB is responsible for developing and delivering products and services that are crucial to the military’s mission, making it a high-value target for cybercriminals and foreign adversaries. The CMMC framework ensures that contractors implement robust cybersecurity standards to protect against threats to national security.
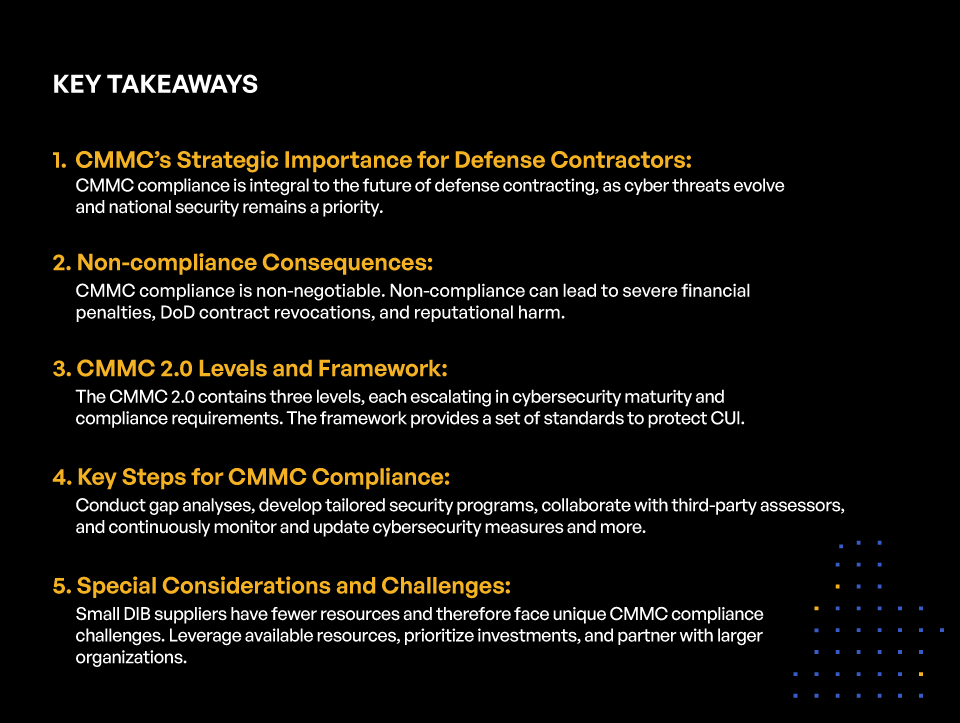
KEY TAKEAWAYS
- CMMC’s Strategic Importance for Defense Contractors:
CMMC compliance is integral to the future of defense contracting, as cyber threats evolve and national security remains a priority. - Non-compliance Consequences:
CMMC compliance is non-negotiable. Non-compliance can lead to severe financial penalties, DoD contract revocations, and reputational harm. - CMMC 2.0 Levels and Framework:
The CMMC 2.0 contains three levels, each escalating in cybersecurity maturity and compliance requirements. The framework provides a set of standards to protect CUI. - Key Steps for CMMC Compliance:
Conduct gap analyses, develop tailored security programs, collaborate with third-party assessors, and continuously monitor and update cybersecurity measures and more. - Special Considerations and Challenges:
Small DIB suppliers have fewer resources and therefore face unique CMMC compliance challenges. Leverage available resources, prioritize investments, and partner with larger organizations.
CMMC 2.0 Levels Explained
The CMMC 2.0 framework is designed to provide a comprehensive, flexible, and scalable set of cybersecurity standards that can adapt to the evolving cybersecurity threat landscape. The framework consists of three levels of security maturity that build upon each other, with each level containing a set of requirements across different domains.
CMMC 2.0 Level 1 (Foundational)
Level 1 (Foundational) is the first level of the CMMC 2.0 framework. The primary purpose of CMMC 2.0 Level 1 is to ensure that organizations have the basic controls in place to protect FCI from unauthorized use. Level 1 is comprised of the 15 basic safeguarding requirements specified in Federal Acquisition Regulation (FAR) Clause 52.204-21
CMMC 2.0 Level 2 (Advanced)
Level 2 (Advanced) is the second level of the CMMC 2.0 framework. It is an intermediate level that requires companies to implement more specific practices to protect CUI. Companies must demonstrate that they are following the best practices in their industry when it comes to cybersecurity. A total of 110 practices must be implemented at this level, which includes configuration management, incident response, identification and authentication, and maintenance.
CMMC 2.0 Level 3 (Expert)
Level 3 (Expert) is the highest level of the CMMC 2.0 framework. It requires companies to have an in-depth understanding of the cybersecurity best practices to protect CUI. For Level 3, there are 134 required controls (110 from NIST SP 800-171 and an additional 24 from NIST SP 800-172). These controls are a means of managing risk that includes policies, procedures, guidelines, practices, or organizational structures, which can be of an administrative, technical, management, or legal nature, and are specified by NIST SP 800-171, NIST SP 800-172, and FAR 52.204-21. These practices sit under 14 different domains that are a subset of NIST SP 800-172. CMMC 2.0 requires the contractor to go beyond mere documentation of processes and instead have an active role in the management and implementation of the controls in order to provide the highest level of security possible.
CMMC Compliance Guide for DIB Suppliers
For DIB suppliers preparing for CMMC accreditation, we suggest the following 12 step guide to ensure their journey is successful:
1. Assess Your Current State of Compliance
Before you can begin building a CMMC-compliant security program, you must assess your current state of compliance. A gap analysis is a useful tool for identifying areas of improvement and establishing a plan of action. The gap analysis should focus on the security requirements and practices in each of the levels of the CMMC framework to identify gaps in your current cybersecurity measures.
Once you have identified these gaps, you can begin to prioritize them and establish a plan of action to remediate them. This plan should include timelines for implementation, responsible parties, and milestones. It is essential to involve key stakeholders in the planning process to ensure buy-in and collaboration across the organization.
2. Build a CMMC-compliant Security Program
Building a CMMC-compliant security program involves several steps, including developing policies and procedures, implementing access controls, securing systems and networks, and conducting regular security assessments.
Developing policies and procedures is a critical first step in building a CMMC-compliant security program. Policies and procedures should be tailored to your organization’s needs and should reflect the requirements of the CMMC framework.
Implementing access controls is also essential to building a CMMC-compliant security program. Access controls should ensure that only authorized individuals have access to sensitive data and that access is granted based on a need-to-know basis.
Securing systems and networks is another critical aspect of building a CMMC-compliant security program. This includes all hardware and software systems, including servers, workstations, and mobile devices. Security measures should include firewalls, antivirus software, intrusion detection and prevention systems, and regular software updates.
Conducting regular security assessments is also essential to maintaining a CMMC-compliant security program. These assessments should occur regularly and should include vulnerability scans, penetration testing, and risk assessments.
3. Prepare for a CMMC 2.0 Audit
Preparing for a CMMC 2.0 audit involves several steps, including understanding the audit process, working with a third-party assessor, and tips for a successful audit.
Understanding the audit process is critical to preparing for a CMMC 2.0 audit. The audit process involves a third-party assessor evaluating your organization’s compliance with the CMMC framework. The assessment typically includes a review of policies and procedures, interviews with employees, and a technical assessment of systems and networks.
Working with a third-party assessor is required for CMMC 2.0 certification. Organizations should carefully select an assessor with experience and expertise in the CMMC framework. It is essential to establish a positive working relationship with the assessor and provide them with all necessary documentation and access to conduct the assessment.
Tips for a successful audit include ensuring that all policies and procedures are up to date and that employees are aware of their roles and responsibilities. It is also essential to regularly conduct security assessments and address any vulnerabilities that are identified promptly. Finally, organizations should be transparent with the assessor and provide all necessary documentation to support compliance with the CMMC framework.
4. Maintain CMMC Compliance
Maintaining CMMC compliance involves ongoing monitoring and testing, reassessment, and recertification, and handling security incidents.
Ongoing monitoring and testing are critical to maintaining CMMC compliance. Organizations should perform regular vulnerability scans, penetration testing, and risk assessments to identify potential security threats and weaknesses. Regular monitoring of systems and networks can also help detect and prevent security incidents.
Reassessment and recertification are necessary to maintain CMMC compliance. CMMC 2.0 certification is valid for three years, after which organizations must undergo reassessment and recertification to maintain compliance.
Handling security incidents is also essential to maintaining CMMC compliance. Organizations should have a plan in place to detect and respond to security incidents promptly. This should include procedures for reporting incidents and mitigating their impact.
5. Adopt an Entrepreneurial Mindset, Especially if You’re a Small or Medium-sized Supplier
Navigating the CMMC 2.0 compliance process can be particularly challenging for small and medium-sized suppliers. These organizations may have limited resources, making it difficult to implement robust cybersecurity measures. However, there are several resources and support available to assist small and medium-sized suppliers in achieving CMMC compliance.
Special considerations for smaller companies include prioritizing cybersecurity investments, leveraging available resources such as the Cybersecurity Maturity Model Certification Center of Excellence, and partnering with larger organizations that can provide guidance and support. Additionally, some CMMC assessors specialize in working with smaller organizations and can provide tailored assessments and guidance.
6. Communicate the Benefits of CMMC Compliance
CMMC compliance offers several benefits to Defense Industrial Base suppliers, including competitive advantages, strengthened cybersecurity defenses, and opportunities for growth and collaboration.
One of the significant advantages of CMMC compliance is that it provides a competitive edge in the DIB supply chain. CMMC compliance demonstrates a commitment to cybersecurity and protects against the risks of cyberattacks and data breaches. Compliance can also open doors to new business opportunities and partnerships with other organizations that prioritize cybersecurity.
Moreover, CMMC compliance strengthens cybersecurity defenses by ensuring that contractors implement robust security measures that meet the requirements of the framework. Compliance reduces the risk of cyberattacks and data breaches, protecting sensitive information and national security.
Finally, CMMC compliance presents opportunities for growth and collaboration within the DIB supply chain. Collaboration with upstream and downstream partners can ensure compliance throughout the supply chain, reducing the risk of cyber incidents and increasing supply chain resilience.
7. Understand Common Misconceptions About CMMC Compliance
There are several common misconceptions about CMMC compliance that can create confusion and misinterpretation of guidelines. Separating fact from fiction is crucial to understanding the requirements and importance of CMMC compliance.
One of the most common misconceptions is that CMMC is only applicable to defense prime contractors. However, CMMC compliance is mandatory for all DIB suppliers, including subcontractors and suppliers.
8. Promote CMMC Compliance in the Supply Chain
Collaborating with upstream and downstream partners is essential to ensuring compliance throughout the supply chain. Each organization in the supply chain is responsible for implementing and maintaining cybersecurity measures to protect sensitive information and national security.
CMMC compliance requirements must be communicated clearly and effectively throughout the supply chain. Contracts and agreements should include clear language regarding compliance expectations and consequences for noncompliance.
Finally, organizations must regularly monitor and verify the cybersecurity measures of their supply chain partners to ensure ongoing compliance.
9. Learn How CMMC Impacts International Suppliers
The implications of CMMC compliance for foreign companies can be complex. However, foreign companies that wish to work with the DIB must comply with the framework’s requirements.
Steps for compliance as an international supplier include understanding the requirements of the framework, selecting an appropriate third-party assessor, and understanding the implications of compliance on the organization’s operations.
10. Consider CMMC Compliance for Non-traditional Defense Contractors
Non-traditional defense contractors, such as research institutions and universities, may face unique challenges in achieving CMMC compliance. However, compliance is essential for organizations that handle sensitive information and contribute to national security.
Expanding the scope of CMMC compliance to non-traditional contractors requires addressing unique challenges, such as limited resources and complex organizational structures. It is crucial to involve key stakeholders and establish clear roles and responsibilities for compliance.
11. Consider Complementary Data Protection Regulations
CMMC compliance overlaps with other data protection regulations, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), in several different ways.
First, all three frameworks emphasize the importance of data protection, albeit with differing primary focuses. CMMC 2.0 aims to safeguard CUI and FCI, while GDPR and CCPA focus on personal data protection. However, since CUI and FCI may include personal information, organizations must implement strong security controls for both cybersecurity and data privacy.
Second, both CMMC 2.0 and the data privacy regulations mandate organizations to establish documented policies, procedures, and technical measures to ensure data security. This includes the implementation of access controls, encryption, incident response plans, and continuous monitoring.
Finally, CMMC 2.0, GDPR, and CCPA all require organizations to demonstrate compliance by undergoing assessments and audits. CMMC 2.0 involves a third-party certification process, while GDPR and CCPA necessitate privacy impact assessments and adherence to privacy-by-design principles. By aligning these various regulatory requirements, companies can ensure a robust and comprehensive approach to cybersecurity and data privacy, thereby minimizing risks and safeguarding stakeholder trust.
12. Anticipate Changes to CMMC Compliance and Defense Contracting
CMMC compliance is a critical component of the future of defense contracting. As cyber threats continue to evolve, the DoD will continue to implement rigorous cybersecurity standards to protect national security.
Preparing for evolving security requirements involves staying up to date on changes to the CMMC framework, establishing a culture of cybersecurity, and prioritizing ongoing training and education for employees.
Accelerate CMMC Compliance With Kiteworks
Kiteworks ensures regulatory compliance and effectively manages risk with every send, share, receive, and save of sensitive content. The Kiteworks Private Content Network is FedRAMP Moderate Authorized and supports nearly 90% of Level 2 requirements for CMMC compliance. This removes many of the CMMC barriers facing contractors and subcontractors that conduct business with the DoD, enabling them to demonstrate CMMC 2.0 compliance in weeks versus months.
How Kiteworks Supports CMMC Compliance
The Kiteworks Private Content Network (PCN) helps organizations reduce the cost, administration, and complexity by deploying a single platform to protect and manage the breadth of content communications, including encrypted email, file sharing, SFTP, managed file transfer (MFT), forms, and custom enterprise integrations, with no file size limitations.
Some of the core capabilities in Kiteworks that enable rapid CMMC 2.0 compliance include:
- Consolidation of secure email, file sharing, file transfer, managed file transfer, web forms, and application programming interfaces (APIs) into one platform that unifies metadata
- Certification with key U.S. government compliance standards and requirements that include FedRAMP and SOC 2
- Validated by the NIST for FIPS 140-2 compliance
- Enable sensitive content communications compliance with regulations and standards such as NIST SP 800-171 and NIST SP 800-172, among others
- FedRAMP Authorized for Moderate Level Impact provides out-of-the-box compliance with CMMC 2.0 Level 2 and over 300 governance controls
- Protects CUI with enterprise-grade security such as file-level AES-256 encryption
- Single point of integration for security investments used to protect sensitive data communications under CMMC 2.0 practices
- Trusted solution engineers and customer success managers and specialists to help design and manage security and compliance in Private Content Networks
DoD contractors and subcontractors looking to achieve CMMC 2.0 Level 2 accreditation ahead of their competitors need to take a serious look at Kiteworks. Schedule a custom demo tailored to your needs today.
Frequently Asked Questions
CMMC 2.0 is an update to the Cybersecurity Maturity Model Certification (CMMC) that was initially released in January 2021. It is the Department of Defense’s (DoD) method for requiring organizations in the DoD supply chain to protect federal contract information (FCI) and controlled unclassified information (CUI) to the appropriate level determined (there are three levels in CMMC 2.0). CMMC 2.0 is a restructure of CMMC’s maturity levels by eliminating two of the original five ratings, improved assessment protocols that reduce costs for contractors, and the introduction of a more flexible path to certification through Plans of Action & Milestones (POA&Ms)
Compliance with NIST standards are levied as contractual requirements through inclusion of clauses such as FAR 52.204-21 and DFARS 252.204-7012. CMMC requirements result in a contractor self-assessment, or a third-party assessment by a CMMC Third Party Assessor Organization (C3PAO), to determine whether the applicable NIST standard (as identified by the DFARS clause) has been met. Under CMMC 2.0, a Level 2 assessment will be conducted against the NIST SP 800-171 standard and a Level 3 assessment will be based on a subset of NIST SP 800-172 requirements.
CMMC C3PAO is a CMMC Third Party Assessor Organization (C3PAO) authorized and certified by the CMMC Accreditation Body (CMMC-AB) to conduct assessments of contractors and subcontractors seeking certification to demonstrate compliance with the CMMC standard. C3PAOs are entrusted with assessing and certifying that companies in the defense industrial base (DIB) supply chain have met the cybersecurity requirements of the CMMC standard. Their responsibilities include evaluating and issuing certificates of adherence to the CMMC standard. The C3PAO must review and certify the contractor or subcontractor’s audit and self-assessment reports based on the DoD’s Cybersecurity Maturity Model. The C3PAO must also be able to recommend and implement corrective actions as needed.
CMMC 2.0 applies to all third parties within the defense supply chain, including contractors, vendors, and any other contracted third parties related to the support of the department of defense (DoD). All civilian organizations that do business with the DoD must comply with CMMC2.0, based on the type of CUI and FCI that they handle and exchange. The list of entities includes:
- DoD prime contractors
- DoD subcontractors
- Suppliers at all tiers in the DIB
- DoD small business suppliers
- Commercial suppliers that process, handle, or store CUI
- Foreign suppliers
- Team members of DoD contractors that handle CUI such as IT managed service providers
According to Kiteworks, working with a CMMC Third Party Assessor Organization (C3PAO) provides several benefits for organizations seeking certification under CMMC 2.0 standards:
- Expertise: A certified third-party assessor has extensive experience assessing cybersecurity programs across multiple industries and can provide valuable insight into best practices for achieving compliance with CMMC 2.0 standards.
- Objectivity: An independent third-party assessor provides unbiased feedback on an organization’s security posture that can help identify areas where improvements are needed.
- Cost Savings: Working with a certified third-party assessor can save time and money compared to hiring internal staff or consultants who may not have expertise in assessing cybersecurity programs.
- Efficiency: A certified third-party assessor can quickly identify gaps in an organization’s security posture, helping to reduce time spent preparing for certification.
- Peace of Mind: Having an independent third-party assessor review a DoD supplier’s cybersecurity program provides peace of mind, ensuring that organizations have taken all necessary steps toward achieving compliance with CMMC 2.0 standards.
Additional Resources
- Blog Post A Roadmap for CMMC 2.0 Compliance for DoD Contractors
- Blog Post Uncovering the Benefits of Working With a C3PAO Organization for CMMC 2.0 Compliance
- Video How CMMC-compliant Content Communications Can Grow Your DoD Business
- Video CMMC 2.0 and Its Impact on the Defense Industrial Base
- White Paper Securing Content Communications for CMMC 2.0