CMMC: Cybersecurity Maturity Model Certification
While CMMC is still evolving, you will want to ensure your business is up to date on what a CMMC certification is and how its updates affect you.
The CMMC certification process is arduous but our CMMC 2.0 compliance roadmap can help.
What is CMMC? Cybersecurity Maturity Model Certification is a standard that requires Department of Defense contractors to meet certain levels of cybersecurity in order to protect the department’s sensitive data.

What Is CMMC?
The Cybersecurity Maturity Model Certification (CMMC) is a unified standard for safeguarding Controlled Unclassified Information (CUI) within the Defense Industrial Base (DIB). It is a framework used to assess an organization’s cybersecurity practices and allows the Department of Defense (DoD) to certify that these practices meet the requirements set forth in the NIST SP 800-171. The certification is required for all organizations working with the DoD, as CMMC is designed to protect CUI from cyber threats and ensure that contractors follow the same cybersecurity policies and procedures.
What Is the CMMC Framework?
The Cybersecurity Maturity Model Certification (CMMC) is a streamlined and centralized cybersecurity framework created by the U.S. Department of Defense to support contractors in defense supply chain compliance and security efforts.
Understanding the CMMC framework is crucial for defense contractors as it outlines the necessary cybersecurity standards and practices required to protect sensitive data and ensure compliance. CMMC is designed to enhance the defense sector’s security posture by mandating a tiered cybersecurity framework. This framework is essential for contractors working with the DoD and associated agencies, as it specifies the levels of cybersecurity hygiene and processes that must be implemented based on the sensitivity of the data handled.
Unlike previous regulations that allowed contractors to self-certify their cybersecurity measures, the CMMC framework introduces a tiered system of compliance, ranging from basic cyber hygiene requirements to advanced security protocols, ensuring that all defense contractors meet a baseline of cybersecurity standards to protect both unclassified and controlled unclassified information critical to national security.
Introduced in 2019, the CMMC framework was established to enhance the cybersecurity posture of defense contractors, ensuring they have the required levels of security to protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). Differing from the previous self-certification process under NIST 800-171 guidelines, the CMMC framework mandates a third-party assessment to validate compliance, answering the vital question of “what is CMMC” by setting a structured benchmark for cybersecurity readiness and resilience within the defense industrial base.
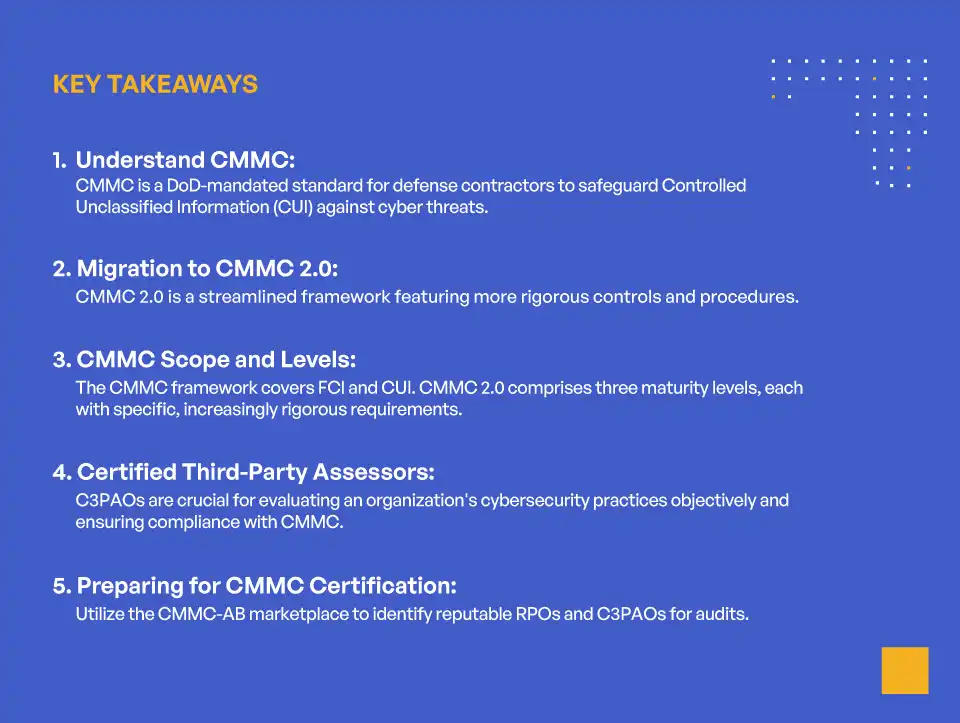
KEY TAKEAWAYS
- Understand CMMC:
CMMC is a DoD-mandated standard for defense contractors to safeguard Controlled Unclassified Information (CUI) against cyber threats. - Migration to CMMC 2.0:
CMMC 2.0 is a streamlined framework featuring more rigorous controls and procedures. - CMMC Scope and Levels:
The CMMC framework covers FCI and CUI. CMMC 2.0 comprises three maturity levels, each with specific, increasingly rigorous requirements. - Certified Third-Party Assessors:
C3PAOs are crucial for evaluating an organization’s cybersecurity practices objectively and ensuring compliance with CMMC. - Preparing for CMMC Certification:
Utilize the CMMC-AB marketplace to identify reputable RPOs and C3PAOs for audits.
The CMMC framework marks a pivotal shift in how defense contractors ensure cybersecurity compliance. Previously reliant on self-attestations, the CMMC framework introduces a structured model that necessitates third-party audits to verify compliance with cybersecurity standards. This framework is encapsulated in the interim rule Defense Federal Acquisition Regulation Supplement (DFARS) 2019-D041, integrating CMMC requirements into all defense procurement processes. This transformation underlines the Department of Defense’s commitment to fortifying cybersecurity measures across its supply chain, highlighting the criticality of understanding what CMMC is and its implications for defense contractors.
In November 2021, the DoD unveiled the CMMC 2.0 framework, marking a significant evolution in the cybersecurity standards for defense contractors. We’ll explore in greater detail below the enhancements introduced with the CMMC 2.0 framework.
What is the Scope of the CMMC Framework?
The scope of the CMMC framework covers the security of all Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) stored or handled by a covered contractor’s (organization’s) environment and applies to all activities conducted by the organization. The process and procedures address the security of all areas of the contractor’s organization that process, store, or transmit FCI and CUI, including their networks, systems, personnel, and other assets.
CMMI vs. CMMC: Which One Do Defense Contractors Need?
The Capability Maturity Model Integration (CMMI) is a process improvement approach that provides organizations with the essential elements for effective process improvement. CMMI helps organizations to improve process performance and integrate organizational processes. It is used across a variety of industries, including aerospace, defense, software engineering, finance, government, and healthcare. CMMI is a framework that defines process improvement stages and assesses the maturity of organizations in six key areas of process implementation: performance, project management, services, support, process integration, and organizational process focus.
The Cybersecurity Maturity Model Certification (CMMC), as we’ve discussed, is a certification created by the U.S. Department of Defense (DoD) to better protect unclassified data that is either processed on or stored on DoD contractor and subcontractor networks. CMMC certification is required for DoD contracts, and it is intended to provide an additional layer of security for sensitive data and information systems. CMMC is designed to address the need for additional security controls for DoD contractors and suppliers handling Controlled Unclassified Information (CUI).
The main difference between the CMMI and CMMC is the purpose of each certification. CMMI is a process improvement approach that is used to improve organizational processes and performance, while CMMC is a security certification intended to protect unclassified data stored on DoD contractor and subcontractor networks. CMMI is a process improvement approach and CMMC is a security certification.
Defense contractors should adhere to both CMMI and CMMC in order to increase the security of their systems and ensure they are compliant with all relevant DoD regulations. CMMI will help contractors better manage and improve their processes, while CMMC will protect their networks and unclassified data. Additionally, CMMC also provides a basis for determining whether a defense contractor is meeting their contractual obligations. By adhering to both CMMI and CMMC, defense contractors can protect their networks, data, and systems and protect their reputation.
What’s the Difference Between CMMC Compliance and CMMC Certification?
Is there a difference between CMMC compliance and CMMC certification? How are they different? Which one do you need? If you need both, which one do you need first? CMMC certification vs. CMMC compliance can confuse the uninitiated, so let’s briefly review the two terms below.
CMMC compliance refers to the adherence to the cybersecurity practices and processes outlined in the CMMC framework. It involves meeting the specified requirements for handling and protecting Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) as per the guidelines set by the Department of Defense (DoD). Organizations must align their operations, systems, and security protocols to these standards to ensure they are adequately protecting sensitive information.
Alternatively, CMMC certification is the formal recognition provided to organizations that have successfully undergone an assessment by a Certified Third Party Assessor Organization (C3PAO). This assessment verifies that the organization not only adheres to the requirements but also effectively implements the necessary controls and practices. Achieving CMMC certification demonstrates to the DoD and other stakeholders that the organization’s cybersecurity posture meets the rigorous standards necessary for participation in the defense supply chain.
In essence, compliance is the act of following the required cybersecurity practices, while certification is the acknowledgment that an organization has been independently verified as compliant. The certification process provides an additional layer of assurance to the DoD and other parties that the organization is capable of protecting CUI and FCI at the mandated levels.
What Is CMMC 2.0?
In November 2021, the DoD revised requirements based on feedback from partner organizations and firms undergoing the C3PAO certification process. Their goal with this revision was to streamline the framework to make it less costly and time-consuming for all stakeholders without sacrificing effectiveness.
The proposed changes under version 2.0 include the following:
- Reducing Maturity Levels From Five to Three: Under 2.0, the new model will only include three maturity levels. Level 1 will still be the minimum to handle FCI and require 17 practices from NIST 800-171. Level 2 will be the minimum level for managing CUI and represents a merger of the original second and third levels with a required 110 total practices. Finally, Level 3 will include 110+ required practices (determined by the needs of the client agency).
- Only Limited Requirements for C3PAOs: Rather than require a C3PAO for all contractors, version 2.0 only requires a triannual third-party audit for certification at Levels 2 and 3. Contractors seeking Level 1 certification (and a limited number of those seeking specific Level 2 certifications) can opt for annual self-attestation.
- Plan of Action and Milestones: Some other frameworks included the option for audited contractors to submit a plan of action and milestones (POA&M) at the end of their audits. Suppose their auditor determined that the contract was not fully compliant but could be compliant in a reasonable time frame with relatively simple changes. In that case, they could authorize the contractor with a completed and binding POA&M. CMMC 1.0 did not allow this approach—the contractor had to be fully compliant to receive certification. Under version 2.0, the DoD will allow for POA&Ms under certain conditions.
The CMMC 2.0 model is currently just a publication and undergoing review and rulemaking processes. It is expected to finish that process in 9–24 months. In the meantime, the CMMC-AB still honors and operates under version 1.0 audits and certifications.
What Is a Certified Third Party Assessor Organization?
The other major update from CMMC 1.0 is the requirement of a third-party assessment through a Certified Third Party Assessor Organization (C3PAO).
C3PAOs are critical security firms in defense cybersecurity that have received accreditation from the CMMC Accreditation Body (CMMC-AB) to provide audits of defense contractors. Any organization familiar with other security frameworks like FedRAMP will immediately recognize this process. CMMC borrows some of its auditing process from the same documents, namely NIST 800-53 and FIPS 140-2.
One of the drawbacks to working with a C3PAO is that they cannot also serve as a consultant with your organization. That’s why there is a secondary designation under regulations—the Registered Provider Organization (RPO). An RPO can provide consulting, recommendations, and advice to clients who are preparing for their compliance journey. The same security firm can never serve as both an RPO and a C3PAO for a single organization.
CMMC 1.0 vs. 2.0: Key Differences
One of the primary differences between the CMMC 1.0 and CMMC 2.0 framework is the reduction in the number of maturity levels. CMMC 1.0 featured five levels, whereas CMMC 2.0 consolidates these into three levels: Foundational, Advanced, and Expert. This streamlining aims to simplify the model, making it more accessible and less burdensome for contractors while still maintaining robust security standards.
Another significant change involves the self-assessment option at lower levels. Under CMMC 2.0, organizations seeking Level 1 (Foundational) certification can perform annual self-assessments, reducing the need for third-party audits and the associated costs. For Level 2 (Advanced), a bifurcated approach allows for some self-assessments and some third-party assessments, depending on the sensitivity and criticality of the information being handled. Level 3 (Expert) will still require rigorous third-party assessments, primarily conducted by the DoD.
The introduction of Plans of Action and Milestones (POA&Ms) is another key update in CMMC 2.0. These plans allow contractors to document and prioritize issues that need remediation, providing a structured timeline to achieve full compliance. The inclusion of POA&Ms offers organizations more flexibility and transparency, ensuring that minor deficiencies do not immediately result in non-compliance.
Incorporation of NIST SP 800-171 and NIST SP 800-172 into CMMC 2.0 further highlights the alignment with established federal cybersecurity standards. This integration helps bridge gaps between existing frameworks and the new CMMC model, making it easier for organizations familiar with NIST guidelines to transition to the updated CMMC requirements.
By focusing on these key differences, contractors can better understand the expectations under CMMC 2.0 and take appropriate steps to adjust their cybersecurity strategies. Adapting to these changes not only ensures compliance but also enhances the overall resilience and security posture of organizations within the defense industrial base.
Overview of CMMC 2.0 Security Certification Levels
Understanding the different CMMC certification, or CMMC maturity, levels is pivotal for organizations aiming to comply with DoD’s cybersecurity requirements. The CMMC 2.0 framework is structured into multiple levels, each building upon the previous to provide a scalable cybersecurity framework that meets varying degrees of cybersecurity maturity and protection. CMMC 2.0, the latest version of the framework, simplifies the original model by reducing the number of levels from five to three, making it more streamlined and cost-effective without compromising on security. The CMMC 2.0 security certification levels are summarized below:
- Level 1 (Foundational) focuses on basic cyber hygiene practices and is primarily aimed at contractors handling Federal Contract Information (FCI). CMMC Level 1 requirements are derived from FAR 52.204-21 and include 17 practices that should be relatively straightforward for most organizations to implement.
- Level 2 (Advanced) is designed as an intermediate step for organizations that handle Controlled Unclassified Information (CUI). CMMC Level 2 requires compliance with a subset of the practices outlined in NIST SP 800-171, totaling 110 practices. The goal is to ensure that organizations have more robust cybersecurity measures in place to protect sensitive information.
- Level 3 (Expert) targets organizations handling the most sensitive data and involves compliance with a comprehensive set of practices that builds upon NIST SP 800-171 and includes additional guidance from NIST 800-172. CMMC Level 3 is intended to provide the highest level of cybersecurity assurance and involves a rigorous assessment process conducted by a Certified Third Party Assessor Organization (C3PAO).
Understanding these levels is essential for defense contractors to determine the necessary steps for achieving compliance, securing their operations, and ensuring they can continue to participate in DoD contracts.
Best Practices for CMMC Certification Preparation
Achieving CMMC certification can be a complex and resource-intensive process. To streamline the certification journey and enhance the likelihood of success, organizations should adopt several best practices:
- Perform a Thorough Gap Analysis: Conduct a detailed gap analysis to understand the current cybersecurity posture of the organization. Identify gaps between existing practices and CMMC requirements. Use the findings to prioritize remediation efforts, focusing on critical vulnerabilities and deficiencies first.
- Engage a Registered Provider Organization (RPO): Partner with an RPO to benefit from their expertise in CMMC requirements and best practices. They can provide valuable insights, training, and support throughout the preparation process. Leverage the RPO’s experience to develop customized solutions that fit the specific needs and context of the organization.
- Implement Robust Policies and Procedures: Ensure all cybersecurity policies, procedures, and practices are well-documented and aligned with CMMC requirements. This includes access control, incident response, risk management, and continuous monitoring. Maintain consistency in the implementation and documentation of these practices across the organization.
- Conduct Regular Training and Awareness Programs: Regularly train employees on cybersecurity best practices, CMMC requirements, and their specific roles in maintaining security. Ongoing security awareness training campaigns keep cybersecurity top of mind for all employees, fostering a cyber awareness culture within the organization.
- Leverage Technology and Tools: Utilize advanced cybersecurity tools and technologies to automate and streamline compliance activities. This can include vulnerability management systems, security information and event management (SIEM) solutions, and endpoint protection. Implement continuous monitoring tools to detect and respond to security incidents promptly.
- Regularly Review and Update Practices: Establish a process for regularly reviewing and updating cybersecurity practices to adapt to new threats and changes in the regulatory landscape. Conduct internal mock audits and readiness assessments to ensure ongoing compliance and readiness for the formal CMMC assessment.
By following these best practices, organizations can effectively streamline the CMMC certification process, ensuring thorough preparation, robust cybersecurity posture, and a higher likelihood of achieving the desired certification level. Engaging expert guidance, maintaining comprehensive documentation, and fostering a culture of continuous improvement are key to navigating the complexities of CMMC certification successfully.
The CMMC Framework: Critical Compliance for National Defense
The CMMC compliance is an essential component for any contractor within the defense industrial base supply chain, ensuring that their technology, processes, personnel, and overall operations adhere to stringent cybersecurity standards. CMMC should be viewed as (much) more than a regulatory hurdle; it embodies a comprehensive security protocol that enhances a business’s cybersecurity defenses, resources, and maturity. Achieving compliance with the CMMC framework not only fulfills a critical requirement but also significantly bolsters a business’ cybersecurity posture, securing its position within the defense sector’s supply chain.
The Kiteworks Private Content Network, a FIPS 140-2 Level validated secure file sharing and file transfer platform, consolidates email, file sharing, web forms, SFTP, managed file transfer, and next-generation digital rights management solution so organizations control, protect, and track every file as it enters and exits the organization.
Kiteworks supports nearly 90% of CMMC 2.0 Level 2 requirements out of the box. As a result, DoD contractors and subcontractors can accelerate their CMMC 2.0 Level 2 accreditation process by ensuring they have the right sensitive content communications platform in place.
With Kiteworks, DoD contractors and subcontractors unify their sensitive content communications into a dedicated Private Content Network, leveraging automated policy controls and tracking and cybersecurity protocols that align with CMMC 2.0 practices.
Kiteworks enables rapid CMMC 2.0 compliance with core capabilities and features including:
- Certification with key U.S. government compliance standards and requirements, including SSAE-16/SOC 2, NIST SP 800-171, and NIST SP 800-172
- FIPS 140-2 Level 1 validation
- FedRAMP Authorized for Moderate Impact Level CUI
- AES 256-bit encryption for data at rest, TLS 1.2 for data in transit, and sole encryption key ownership
Kiteworks deployment options include on-premises, hosted, private, hybrid, and FedRAMP virtual private cloud. With Kiteworks: control access to sensitive content; protect it when it’s shared externally using automated end-to-end encryption, multi-factor authentication, and security infrastructure integrations; see, track, and report all file activity, namely who sends what to whom, when, and how. Finally demonstrate compliance with regulations and standards like GDPR, HIPAA, CMMC, Cyber Essentials Plus, IRAP, and many more.
To learn more about Kiteworks and CMMC certification, schedule a custom demo today.