
Five Best Practices to do Supply Chain Security Right
attacks aren’t new. In fact, The National Institute of Standards and Technology (NIST) published their initial report on supply chain risk back in 2015.
One of the most well-known supply chain attacks happened shortly after in 2017. NotPetya corrupted third-party software, initially using a backdoor, and distributed ransomware only a few months later to inflict serious harm on organizations all over the world.
Unfortunately, discussion focused primarily on the ransomware aspect, missing completely the original supply chain attack—a backdoor deployed across thousands of organizations for multiple months.
“The potential for catastrophic supply chain attacks is mind-boggling when you consider a typical organization does business with hundreds, if not thousands, of third parties.”
SolarStorm, the most impactful supply chain attack to date, or more accurately labeled by its technical term “advanced persistent threat,” was a milestone event because it sabotaged a popular software product at the source code level and allowed the attackers to exfiltrate the crown jewels from multiple high-profile organizations across the security, technology, and government sectors. Unfortunately, we still don’t know the full extent of the damage sustained and the hackers have hidden their tracks so well that we may never know for sure.
The potential for catastrophic supply chain attacks is mind-boggling when you consider a typical organization does business with hundreds, if not thousands, of third parties. Work with an outsourced payroll processing company? You’re at risk. Contract with a digital marketing agency? Be careful. Collaborate with channel partners over a cloud platform? Beware of unforeseen and undetected attacks.
The question isn’t whether your organization’s cyber threat vectors are expanding. You already know the answer is “yes.” The real question is what do you do about it?
Five Key Supply Chain Security Best Practices
Unless you can hire an army of security analysts, subscribe to every threat-detection service, buy every security tool on the market, or stay off the digital grid, you need to understand how to detect cyberattacks, protect against them, and properly remediate their impact.
Here are five cybersecurity principles every business leader should know, and be ready to press your CISO, CIO, or CTO about to mitigate a supply chain attack:
-
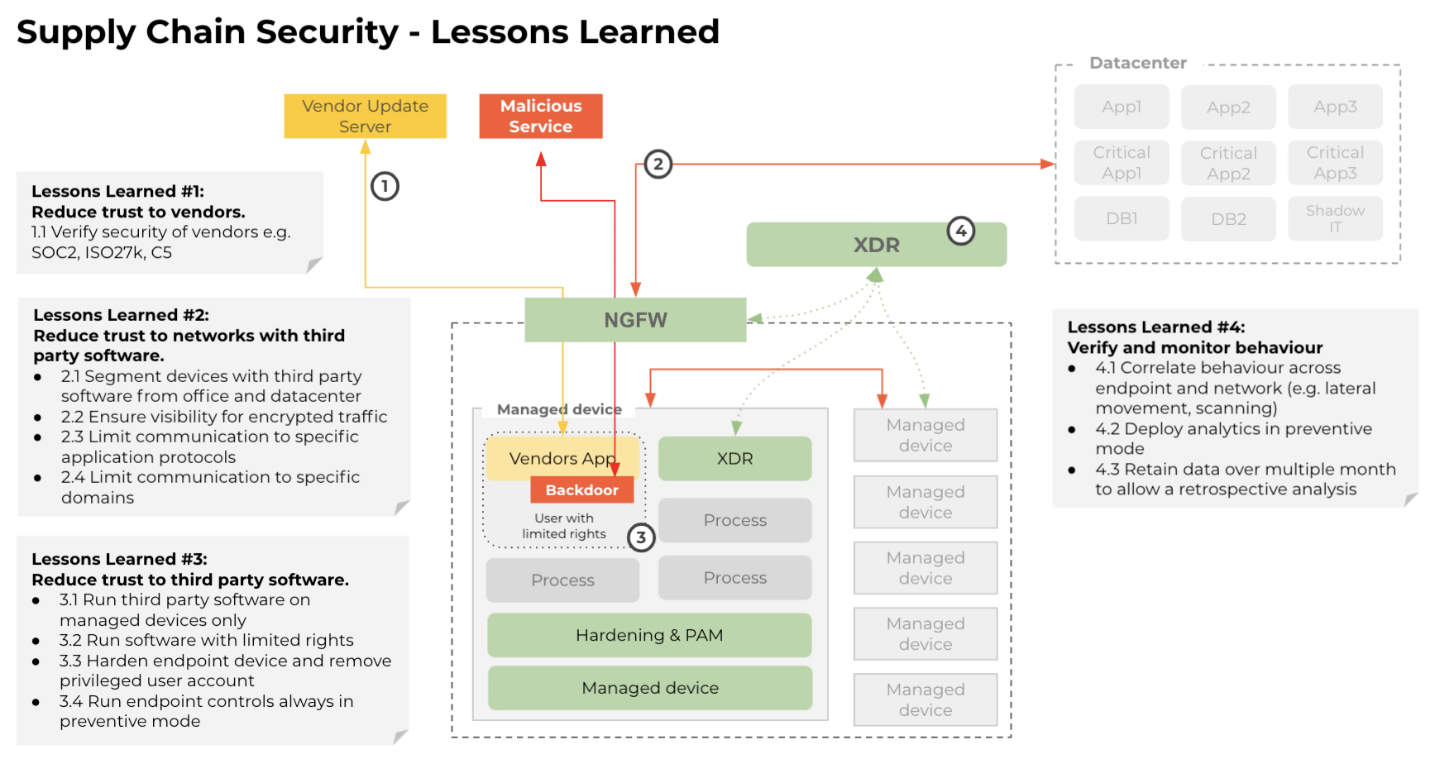
Validate your vendors’ cybersecurity hygiene and practices. Although many large organizations have some safeguards in place to verify their vendors’ security maturity, my experience in working with countless organizations is that few, if any, check all the boxes when it comes to confidently vouching for vendor security. If your organization does not have a specific vendor risk management procedure, you can start by checking for certifications like Common Criteria, CIS, ISO 27000, and SOC 2.
NotPetya and Solarwinds nevertheless demonstrate that we have to embrace vendor risk management more broadly than ever before. We must measure cyber risk not only for vendors who process our data or in outsourcing scenarios, but for every single small application or IoT device in the network requiring connectivity to the cloud. The question isn’t whether your organization’s cyber threat vectors are expanding. You already know the answer is “yes.” The real question is what do you do about it?
-
Take a long, hard look at automated patching policies and procedures. You can actually hear users and executives moan and groan about business disruption every time they receive a security patch notification. Automated patching policies and procedures ensure patches are applied in a timely manner. You should nevertheless study your organization’s automated patching because, if not implemented and managed properly, attackers have an easier time hacking into your organization.
On the other hand, validating patches before deployment does not guarantee you’re protected, given the amount of work required to do it. Instead, you should assume that automated patching will not only continue, but likely will increase. Be sure your CISO is taking extra steps to validate the integrity of automated patching.
The question isn’t whether your organization’s cyber threat vectors are expanding. You already know the answer is “yes.” The real question is what do you do about it?”
-
Commit to Zero Trust. The days of easy access to privileges and lax enforcement of access policies must end. Zero Trust—just like it sounds—is the big vision and should be your organization’s cybersecurity bedrock. Start by reducing the number of privileged users and access to applications, services, and data, especially when it comes to third-party software that is increasingly prevalent in the organization.
To get a better situational awareness, ask your organization a simple question: What is the number of assets or applications a cloud-connected third-party software can reach within our network once it’s been compromised? The answer will determine whether your technical cybersecurity programs like privileged access management, segmentation, and hardening controls are being prioritized relative to the actual risk.
-
Control security at the endpoint. “Shadow IT” makes organizations quite susceptible to supply chain attack. Smart, resourceful end-users have long been bypassing IT approval (and IT security controls) to put in place their own systems and applications. Shadow IT risk dramatically accelerates as younger users (i.e., more technically comfortable and more impatient with IT backlogs) join the organization.
Unsanctioned devices and applications could be malicious, or easily compromised, representing a time bomb for not only the user and device, but to the entire organization. Endpoint security has historically been the most effective line of defense against cyberattacks focused on Shadow IT usage. Consequently, organizations must enforce endpoint security for all devices being connected to the network and controlled by the end-users with no exceptions.
“What is the number of assets or applications a cloud connected third-party software can reach within our network once it’s been compromised?”
-
Leverage digital forensics. Traditional incident response tactics are no longer sufficient as targeted attacks become more sophisticated and more frequent. Having a targeted attacker in your backyard means your business can be massively impacted by espionage or sabotage activities if you don’t get them out immediately. These sophisticated attackers typically leave backdoors, which they use repeatedly over an extended period of time.
Most organizations nevertheless don’t conduct a digital forensics analysis of impacted environments to try and locate hidden backdoors. SolarWinds was clearly a wake-up call to raise awareness of this risk. If you deal with a targeted attack, digital forensics is a must.
While these best practices are cybersecurity-focused, cybersecurity is too big and important to abdicate ownership to any single individual—whether it’s your chief information security officer (CISO) or equivalent technology executive charged with protecting your organization, data, and people against hackers.
“The only safe assumption you can make about supply chain cybersecurity is that your organization is at risk, and you must do something about it now—not after a breach happens.”
To keep an organization safe and resilient, cybersecurity ultimately is the responsibility of the entire C-suite and the board of directors. A CEO doesn’t ignore financial, engineering, marketing, or legal issues because he or she has functional executives overseeing those areas. The same argument applies to cybersecurity.
The only safe assumption you can make about supply chain cybersecurity is that your organization is at risk, and you must do something about it now—not after a breach happens.
Frequently Asked Questions
Regulatory compliance refers to the adherence to laws, regulations, guidelines, and specifications relevant to an organization’s business processes. Compliance is crucial for maintaining the company’s reputation, avoiding legal penalties, and ensuring the safety and security of operations.
Regulatory compliance affects different industries in various ways, depending on the specific regulations applicable to each industry. For instance, healthcare organizations must comply with regulations like HIPAA that protect patient data, while financial institutions must adhere to regulations like the PCI DSS that aim to prevent financial crises. Department of Defense contractors must comply with CMMC. Non-compliance can result in severe penalties, including fines and reputational damage.
Some common challenges include keeping up with changing regulations, managing and securing data, training employees on compliance requirements, and allocating sufficient resources for compliance activities. Additionally, global organizations may face the added complexity of complying with regulations in multiple jurisdictions.
Organizations can demonstrate their compliance with regulations through various means, such as maintaining comprehensive documentation of their compliance activities, conducting regular audits, and providing training records. In addition, some regulations may require organizations to submit regular reports or undergo external audits to demonstrate their compliance.
Data encryption plays a crucial role in regulatory compliance as it helps protect sensitive data from unauthorized access. Many regulations require organizations to implement appropriate security measures, including encryption, to safeguard data. By encrypting data, organizations can ensure its confidentiality and integrity, thereby helping to maintain compliance.
Additional Resources
- Webinar Addressing the Biggest Gap in Your Zero-Trust Strategy
- Report Benchmark Your Sensitive Content Communications Privacy and Compliance
- Blog Post Kiteworks Utilizes Its Own Private Content Network
- Glossary What is Risk Security?
- Glossary What is the Vendor Risk Management Maturity Model?
- GlossaryWhat is Supply Chain Risk Mitigation?
- Glossary What is Managing Third-Party Risk?
- Glossary What is IRM (Integrated Risk Management)?