Digital Rights Management (DRM): Protecting Intellectual Property in the Information Age
The evolution of the internet, including the emergence of smartphones, live streaming, social media, and other technologies and platforms, has created an unprecedented amount of digital content at our fingertips. Moreover, while this has been a boon for consumers, it has presented significant challenges for intellectual property (IP) holders.

The ease with which digital content can be consumed, copied, shared, and distributed has made it difficult for content creators to protect their work and earn a fair return on their investments. In response to this challenge, digital rights management (DRM) has emerged as a critical tool for protecting IP in the digital age.
In this article, we will explore what digital rights management is, how it works, and its evolution over time. We will also examine the importance of IP protection, the role of digital rights management in encouraging innovation and creativity, and the limitations of DRM. Finally, we will consider the future of DRM and its potential impact on the digital economy.
Avoid These 4 DRM Stumbling Blocks to Protect Your IP
What is Digital Rights Management: DRM Overview
Digital rights management is a technology used by publishers, authors, and creators of digital content to control how their digital content is used, accessed, and distributed. It is a system that is designed to prevent unauthorized access, copying, or sharing of copyrighted digital content, such as software, music, eBooks, and videos. Digital rights management works by encrypting the digital content so that only authorized users can access it, and restricting how it can be used and distributed. It is often used to prevent piracy and ensure that content creators receive fair compensation for their work. The term “piracy,” in the context of digital rights management and copyright infringement, refers to the unauthorized copying, distribution, or use of copyrighted materials such as software, music, movies, books, or other digital content. This is done without the permission of the copyright owner or without paying the required fees for its use.
DRM Protected Content Examples
From the latest blockbuster movies and binge-worthy TV series available on platforms like Netflix and Amazon Prime Video, to the chart-topping music albums and singles accessible through Spotify and Apple Music, DRM ensures these creations are safeguarded against unauthorized distribution and piracy. Of course, there’s also the broad universe of e-books and digital publications, offered by services such as Kindle and Adobe Digital Editions, that also falls under this protective umbrella, guaranteeing authors like Sarah Mass, David Baldacci, Tony Robbins, and Kristin Hannah, as well as publishers like the New York Times and The Economist, retain their rights and revenues. Even video games, software applications, and online educational courses are included, with platforms like Steam and Coursera implementing digital rights management to preserve the integrity and value of digital content.
As more businesses produce and digitize content that needs to be shared with select third party groups like customers and consultants, the scope of intellectual property expands. In turn, so does the opportunity for DRM to protect sensitive content beyond the examples listed above. We’ll explore how businesses are utilizing digital rights management technology to protect sensitive content like contracts, product schematics, and personally identifiable and protected health information (PII/PHI) further in this article.
How Does Digital Rights Management (DRM) Work?
Digital rights management works by creating barriers that prevent digital content from being stolen or misused. The primary function of DRM is to prohibit content copying or limit the number of devices a product can be accessed from. Digital rights management involves using applications that encrypt media, data, eBooks, content, software, or any other copyrighted material. Only those with the decryption keys can access the material.
KEY TAKEAWAYS
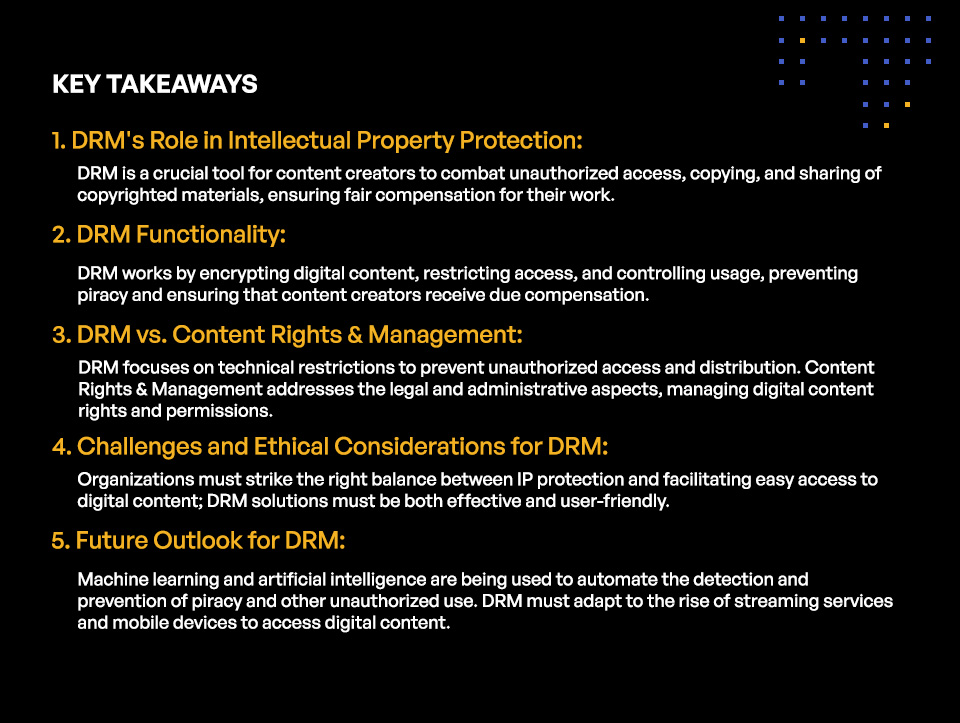
KEY TAKEAWAYS
- DRM’s Role in Intellectual Property Protection:
DRM is a crucial tool for content creators to combat unauthorized access, copying, and sharing of copyrighted materials, ensuring fair compensation for their work. - DRM Functionality:
DRM works by encrypting digital content, restricting access, and controlling usage, preventing piracy and ensuring that content creators receive due compensation. - DRM vs. Content Rights & Management:
DRM focuses on technical restrictions to prevent unauthorized access and distribution. Content Rights & Management addresses the legal and administrative aspects, managing digital content rights and permissions. - Challenges and Ethical Considerations for DRM:
Organizations must strike the right balance between IP protection and facilitating easy access to digital content; DRM solutions must be both effective and user-friendly. - Future Outlook for DRM:
Machine learning and artificial intelligence are being used to automate the detection and prevention of piracy and other unauthorized use. DRM must adapt to the rise of streaming services and mobile devices to access digital content.
DRM allows content creators and copyright holders to restrict or prevent users from editing or saving, sharing or forwarding, printing, or taking screenshots or screengrabs of their content or products. They can also set expiry dates on media, which prevents access to users beyond that date or limits the number of times they can access it. DRM can also limit media access to specific devices, internet protocol (IP) addresses, or locations, such as limiting content to people in the U.S. only. Furthermore, watermarking documents and images can be used to assert ownership and identity of content.
To implement digital rights management, many tools operate through encryption, or computer code embedded in the digital content, to limit access or use. Digital rights management strategies include copy protection and permission management. Copy protection controls access by preventing users from making copies of a work. Examples of these DRM strategies include digital watermarks, fingerprinting, and restricting copying features. Permission management limits who has permission to use a certain work. Examples of these DRM strategies include software licenses and keys, user authentication and IP authentication protocols, proxy servers, virtual private networks (VPNs), regional restriction or geoblocking, and designing products to only work on specialized hardware or software.
Digital Rights Management vs. Content Rights & Management
Digital Rights Management (DRM) and Content Rights & Management share a common goal in protecting digital content but their respective approaches vary in scope. Both DRM and Content Rights & Management play pivotal roles in the protection and monetization of digital content, but their approach and scope differ significantly, catering to varied needs and challenges in the digital landscape. Understanding the differences between Digital Rights Management (DRM) and Content Rights & Management is therefore crucial in safeguarding digital content effectively.
DRM primarily focuses on preventing unauthorized access and distribution of digital media by implementing technical restrictions. It encompasses a variety of control technologies to protect and manage the rights of content owners, ensuring that their digital assets, such as eBooks, music, and videos, are used within the terms of purchase or agreement. On the other hand, Content Rights & Management spans a broader spectrum, encompassing the legal and administrative aspects of managing rights and permissions for digital content. This includes negotiating licensing agreements, copyright management, and ensuring compliance with content distribution policies.
Ultimately, the effectiveness of Digital Rights Management and Content Rights & Management as strategies for content protection and monetization depends on their implementation. While DRM provides technical solutions to safeguard digital assets, Content Rights & Management offers a broader framework for managing those assets in a way that respects the rights of all stakeholders. As the digital content landscape continues to evolve, finding the right balance between these two approaches will be crucial for creators and distributors looking to thrive in a highly competitive and rapidly changing market.
DRM vs. Copyright Protection
Digital Rights Management (DRM) and copyright protection are both mechanisms designed to safeguard the rights of creators and prevent unauthorized use or distribution of digital content. While both aim to protect intellectual property, they differ significantly in their methods and focus.
Copyright protection is a legal framework established to grant creators exclusive rights to their works, including reproduction, distribution, and adaptation. It automatically applies to any original work fixed in a tangible medium of expression, without the need for registration or any specific technology to enforce these rights. Copyright focuses on the legal rights of creators and provides a foundation for them to control and monetize their work.
On the other hand, DRM refers to a set of technical tools and strategies implemented by content providers to control how digital media (e-books, music, movies, etc.) is used and distributed. DRM systems can restrict copying, limit the number of devices on which content can be accessed, or enforce time-based access to content. DRM provides a hands-on approach to enforcing copyright rules, making it a technological extension of the legal protections granted by copyright.
While copyright protection offers a broad, principle-based framework for intellectual property rights, DRM provides specific, enforceable controls on how content is used. DRM can be seen as complementing copyright by adding a layer of practical enforcement to the legal rights already in place. However, DRM is also criticized for being restrictive and potentially limiting legitimate use and fair use of copyrighted material, raising questions about user rights and access to digital content.
Digital Rights Management and Intellectual Property Protection
Digital rights management has emerged as a critical tool for protecting IP. By using encryption and other security measures, DRM makes it more difficult for digital content to be copied, shared, or distributed without permission. This helps to ensure that content creators can earn a fair return on their investment and that consumers can enjoy high-quality digital content without fear of piracy or other unlawful use.
Digital Rights Management vs. Digital Piracy: DRM and the Challenges of Protecting Intellectual Property
It has become easier than ever for consumers to access and share digital content. This has made it difficult for content creators to protect their work and earn a fair return on their investments. The result has been widespread piracy and unlawful use of digital content, which has had a significant impact on the digital economy. For instance, according to the United Nations Office on Drugs and Crime, global counterfeit and pirated goods are estimated to be worth $1.13 trillion annually.
An Argument for DRM: Digital Piracy’s Impact on the Digital Economy
Piracy and unlawful use of digital content have significant consequences for content creators, consumers, and the digital economy as a whole. Piracy can result in lost revenue, decreased investment in new content, and even job losses in the digital content industry. Unlawful use of digital content can also lead to security and privacy risks for consumers. In the U.S. alone, it is estimated that counterfeiting costs between $225 billion to $600 billion each year in lost revenue for businesses.
DRM Pros: Benefits of Digital Rights Management
Digital rights management is an essential tool for content creators and publishers to control access to their digital content and protect their investments, revenues, and profits in return. Incorporating digital rights management technology to protect copyrighted material has many benefits. Here is a list that covers just a few of those benefits:
| Protect Intellectual Property | The primary benefit of DRM is the protection of intellectual property, including music, videos, eBooks, and other digital content. |
| Control Access to Content | DRM provides a means to control access to digital content. It allows content creators to decide who can access their content, how they can use it, and for how long. |
| Generate Revenue | DRM helps content creators generate revenue by controlling access to their digital content. Content creators can monetize their content by selling it to users or through licensing agreements. |
| Reduce Unauthorized Distribution of Content | DRM helps to prevent unauthorized distribution of digital content. It makes it difficult for users to copy or distribute content without permission. |
| Support Compliance With Copyright Laws | DRM helps content creators to comply with copyright laws and prevent piracy of their digital content. |
| Enable Customizable Security Measures | DRM allows content creators to implement customizable security measures to protect their digital content from unauthorized access and copying. |
| Improve User Experience | DRM can improve the user experience by making it easier for users to access and use digital content in a secure and legal manner. |
| Tracking and Analytics | DRM can track usage data and provide analytics to help content creators understand user behavior and preferences. This information can then be used to improve the content and user experience. |
| Innovation and Creativity | DRM plays an important role in encouraging innovation and creativity by protecting the rights of content creators. By ensuring that content creators can earn a fair return on their investment, DRM encourages continued investment in new content and innovation in the digital content industry. |
Digital Rights Management in the Wild: DRM Use Cases
Digital rights management has many use cases but is commonly used in software, computer games, movies, music, and eBooks industries to secure their products. Let’s take a closer look at some of these use cases:
DRM for Protecting Software and Computer Games
Digital rights management is commonly used to protect software and computer games from piracy and other forms of unauthorized use. By using DRM, software and computer game developers can ensure that users have purchased legitimate copies of their products and prevent unauthorized copying and distribution.
DRM for Securing Movies and Music
Digital rights management is also commonly used to secure movies and music from piracy and unauthorized distribution. By using DRM, movie and music producers can ensure that users have purchased legitimate copies of their content and prevent illegal streaming and downloading.
DRM for Preserving the Integrity of eBooks
Digital rights management is increasingly being used to protect eBooks from piracy and unauthorized use. By using DRM, eBook publishers can ensure that users have purchased legitimate copies of their content and prevent unlawful sharing and distribution.
Digital Rights Management’s Detractors: Criticisms of DRM
Digital rights management, like other security technologies, is not bulletproof. There are limitations to what even the best DRM solution can do. Technology shortcomings aside, DRM also poses some complex challenges around “fair use” and consumer rights. Some of these challenges associated with DRM include:
Digital Rights Management and Fair Use: DRM’s Impact on Consumer Rights
Digital rights management has been criticized for its impact on consumer rights. Some critics argue that DRM restricts the ability of consumers to make fair use of digital content, such as sharing content with friends or family members or using content for educational purposes.
Digital Rights Management vs. Users’ Rights: DRM’s Ethical Implications
Digital rights management also raises ethical questions about the balance between the rights of content creators and the rights of consumers. Critics argue that DRM can be overly restrictive and can limit the ability of users to access and use digital content in fair and reasonable ways.
One of the primary ethical issues with digital rights management is that it restricts the rights of users. When DRM is implemented, it limits the ability of users to copy, share, and modify digital content. In some cases, it even prevents users from accessing content on different devices or platforms. This can be seen as a violation of the user’s right to access information and their freedom of expression.
Another ethical issue with DRM is that it undermines the principle of fair use. Fair use allows users to make limited use of copyrighted material without permission from the copyright holder. However, DRM can restrict the ability of users to exercise their fair use rights, which can be seen as an infringement of their rights.
Furthermore, digital rights management can also be seen as an unfair business practice. DRM can limit competition in the digital marketplace by making it difficult for third-party vendors to offer compatible products or services. In addition, DRM can limit consumer choice by forcing users to purchase content from a single vendor or platform.
Digital Rights Management and the User Experience: Striking a DRM Balance Between Protection and Ease of Access
Implementing effective DRM can be challenging, as it requires a balance between protecting intellectual property rights and facilitating easy access and usage of intellectual property. Digital rights management must be easy to use and must not overly restrict the ability of consumers to access and use digital content. If consumers are required to enter a username and password or other special code to access intellectual property, they may be less inclined to use it or recommend it to family and friends.
Digital Rights Management Forecast: the Future of DRM Technology
The future of digital rights management is likely to focus on enhancing intellectual property protection and ease of use. For example, new technologies, such as blockchain-based DRM, are being developed to provide even greater protection for digital content. Other technologies, such as machine learning and artificial intelligence, are being used to automate the detection and prevention of piracy and other unauthorized use.
Adapting DRM to Emerging Trends in Technology and Media Consumption
Digital rights management will need to adapt to emerging trends in technology and media consumption, such as the rise of streaming services and the increasing use of mobile devices to access digital content. DRM technologies will need to be easily integrated with existing systems and devices, and must not overly restrict the ability of consumers to access and use content on their preferred devices.
Potential Impact of Digital Rights Management on the Digital Economy
The potential impact of digital rights management on the digital economy is significant. Effective DRM can encourage continued investment in new content and innovation in the digital content industry, while protecting the rights of content creators and ensuring that consumers have access to high-quality digital content. However, over-reliance on digital rights management can stifle innovation and creativity, and must be balanced against the rights of consumers to access and use digital content in fair and reasonable ways.
Kiteworks’ Next-gen Digital Rights Management Helps Businesses Protect Their Sensitive Content
The Kiteworks Private Content Network (PCN) is a powerful tool that helps businesses protect their intellectual property, particularly as it’s stored and shared with trusted third parties like customers, partners, and suppliers. Document watermarking, for example, makes it difficult for users to distribute sensitive documents and files without naming the file’s origin.
Kiteworks’ revolutionary digital rights management capabilities are designed to be flexible and adaptable to the needs of different organizations. Organizations leverage these DRM capabilities to set and enforce who can access sensitive content according to the specific needs and roles of different users within the organization.
Administrators also have the option to require that file previews are sent as DRM protected files instead of view-only files. This feature can be accessed through a new “Send DRM protected file” item that appears in the dropdown menu next to each file in All Files and in the file viewer.
Kiteworks also includes robust logging and auditing capabilities, so every action related to a DRM protected file is logged and can be audited. This includes when the file was accessed, who accessed it, and what actions they took. This level of detail is crucial for maintaining compliance with various data protection regulations and for investigating any potential security incidents.
Kiteworks’ extensive encryption capabilities make it much harder for unauthorized users to access, view, and share sensitive files. The Kiteworks Email Protection Gateway automatically encrypts files through the entire email journey, even through firewalls. Kiteworks also enables organizations to protect files stored on the platform. For example, role-based access control permissions ensure that only those authorized to access specific documents or files will be able to view, download, or share them. This means that employees can be given access to the information they need for their work, while other sensitive information remains protected.
And before an intended recipient can access a shared file, they must register using multi-factor authentication. This prevents an unauthorized user from accessing sensitive content in the event an email is intercepted or a device is stolen. Kiteworks also offers extensive audit logging, allowing businesses to track who has accessed their information and when. This feature provides companies with a clear picture of their intellectual property and helps them identify potential security breaches or unauthorized access attempts.
Organizations protect their copyrighted material like documents, images, audio or video files, or some other form of sensitive content every time they share it, whether using email, file sharing, managed file transfer, or other communication channel.
