Content-defined Risk Policies
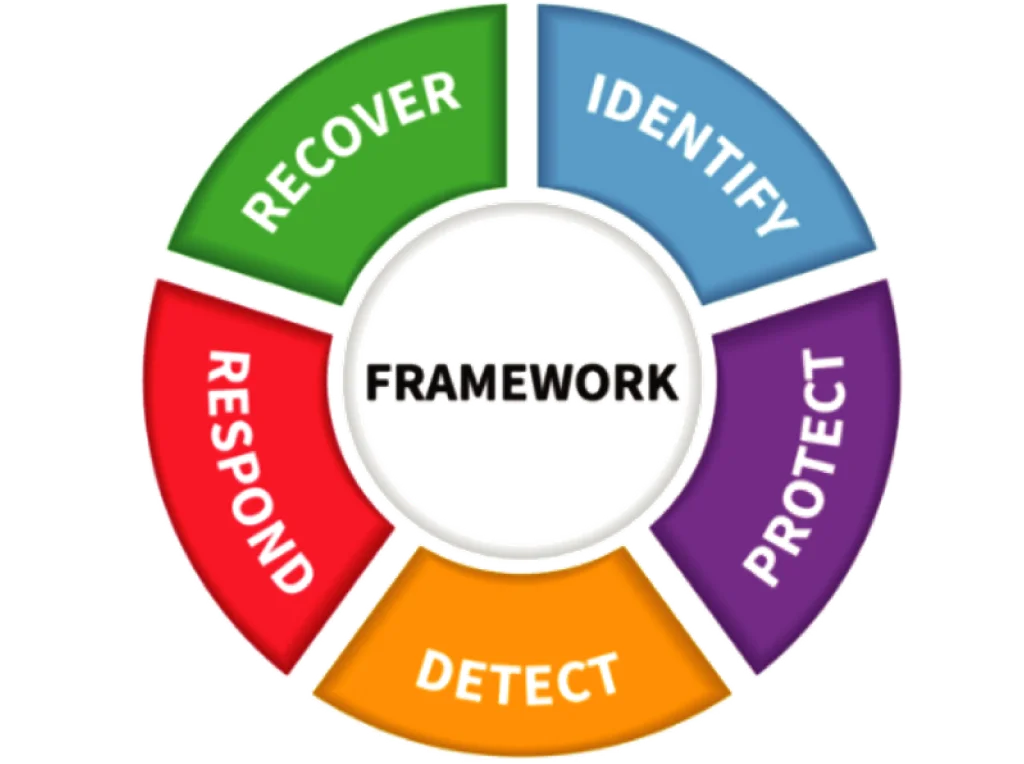
Enforce your NIST CSF controls at the content layer by defining policies with restrictions such as “use SafeEDIT” that Kiteworks applies dynamically in real time. Base each policy on the attributes of the user, the content, and the requested action. Implement unlimited data governance policies with Advanced Governance, or two policies with Kiteworks Enterprise.
Risk Policy Compliance Report
Monitor and evaluate enforcement of your content-defined risk policies, ensuring they trigger appropriately. Your compliance admin can filter data governance events corresponding to a selected policy and time frame to audit precise execution or review policy triggers: see the action requested, user, tags, and files affected. Standard parameters are included too, such as the user’s device, IP address, and geographic location.


CMMC 2.0 Compliance Report
Reduce CMMC audit risk and preparation cost by automatically gathering data governance information for compliance controls. Get an automatic pass/fail status when detectable by the system, fix problems before the audit, and demonstrate CMMC compliance with confidence.
Insider Threat Compliance Report
Defend your data governance efforts by investigating suspicious insider activity, tracking the actions of a suspected user to pinpoint risky behavior. Instantly gather details of communications, files accessed, downloads, and other actions, and assemble the information you need for HR and legal action.

Outsider Threat Compliance Report
In the event of a potential risk or attack coming from an external user outside of an organization, compliance officers can now generate Outsider Threat reports to monitor the activity and communications of external users or domains who have access to the system.
HIPAA Compliance Report
Keep your data governance efforts audit-ready for complete HIPAA compliance with Kiteworks’ one-click reports. Demonstrate implementation of Administrative Safeguards like inactive account controls, Technical Safeguards such as key rotation, Physical Safeguards status per AWS and Azure SOC 2 attestations, and access management details like DLP integration and incident response plans.


GDPR Compliance Report
Ensure your data governance efforts are GDPR-ready with comprehensive visibility of internal and external information exchange in a one-click, audit-ready report. Capture and report who’s sending what to whom, when, from which connected on-premises and cloud content sources, to where. Detailed reports allow for data analysis down to the file level, and show which files have passed or failed AV, DLP, and ATP scans.
Unlimited Message Tracking Dashboards for End-users
Enable users who send email to many users to track the recipients’ access. Employees can instantly pinpoint recipients who have not read or downloaded the content so they can follow up. Save time and tighten processes involving legal notices, billing, negotiations, content reviews, project management, and more. Limited to two dashboards per user with Kiteworks Enterprise, but unlimited with the Advanced Governance add-on.

Legal Hold for eDiscovery
Put a backstop behind your data governance efforts with preservation of all third-party content communications for litigation: files, versions, emails, and activity traces. Secure the content and protect it from spoliation within the Kiteworks hardened virtual appliance to maintain a provable chain of custody that’s transparent to end-users. It supports successful investigations and litigation with detailed reporting, as well as integrations with email archiving and eDiscovery.
DLP Content Scanning, Blocking, and Visibility
Protect your outgoing data from inadvertent or intentional leaks, using your best-in-class DLP solution to identify PII, PHI, IP, or other sensitive information in outgoing files. The Kiteworks platform logs metadata about the content and the DLP result and notifies appropriate admins of all failures. Or you can set it to block sending of failing files, and designate admins who can unlock any false positives. The CISO Dashboard provides the best way to visualize activity in context, drill in with reports, or export to your SIEM.


ATP Scanning, Quarantine, and Visibility
Protect your enterprise from zero-day threats by automatically feeding incoming files through your advanced threat protection (ATP) system. Kiteworks quarantines failing files and notifies appropriate security personnel. All activity is fully logged and visible via reporting and the CISO Dashboard, and exportable to your syslog and SIEM.
Content Disarm and Reconstruction (CDR) and Sanitization Integration
Sanitize incoming content with commercial CDR servers like Forcepoint Zero Trust CDR via ICAP to protect your organization from malware without processing delays or quarantines.
Frequently Asked Questions
Advanced governance is a series of sophisticated approaches and tools for managing, controlling, and optimizing an organization’s data, information assets, and technology systems. Advanced governance tools help organizations manage risk and comply with various regulatory compliance laws by building workflows aligned with frameworks, providing enhanced user experiences to simplify information and records management, and extending governance capabilities beyond specific platforms like Microsoft Office 365 to where information lives and work happens.
Content-based risk policies, also known as content-defined risk policies, are an important component of advanced governance systems that help organizations enforce security controls and compliance requirements at the content layer. These policies are crucial for protecting sensitive data and maintaining regulatory compliance.
Advanced governance enhances businesses’ data protection efforts by through AI-driven data classification, automated policy enforcement, and intelligent retention. Advanced governance tools also provide centralized control across various platforms, offer risk assessment tools, and deliver granular visibility of sensitive information, namely where it’s stored and who has access to it. By automating these and other aspects of data protection, advanced governance reduces administrative burden while improving accuracy in identifying risks to a business’ sensitive content.
Advanced governance aids businesses in demonstrating regulatory compliance by automating data classification, policy enforcement, and reporting aligned with regulations like GDPR and HIPAA. It provides customizable workflows, maintains audit logs, and streamlines eDiscovery for legal hold processes, enabling efficient data management and quick responses to regulatory inquiries. This comprehensive approach allows organizations to produce compliance evidence easily during audits.
Content governance, in the context of data protection and regulatory compliance, is the systematic management of digital content throughout its lifecycle to ensure security, privacy, integrity, and adherence to regulations. It involves establishing policies and procedures, implementing access controls and encryption, maintaining audit logs for content access, ensuring compliance with data protection laws like GDPR and CCPA, and regular auditing and updating of governance practices.
FEATURED RESOURCES

Empowering Robust Private Content Management With Kiteworks Advanced Governance

