Govern Every Sensitive Data Exchange With the Kiteworks Data Control Plane
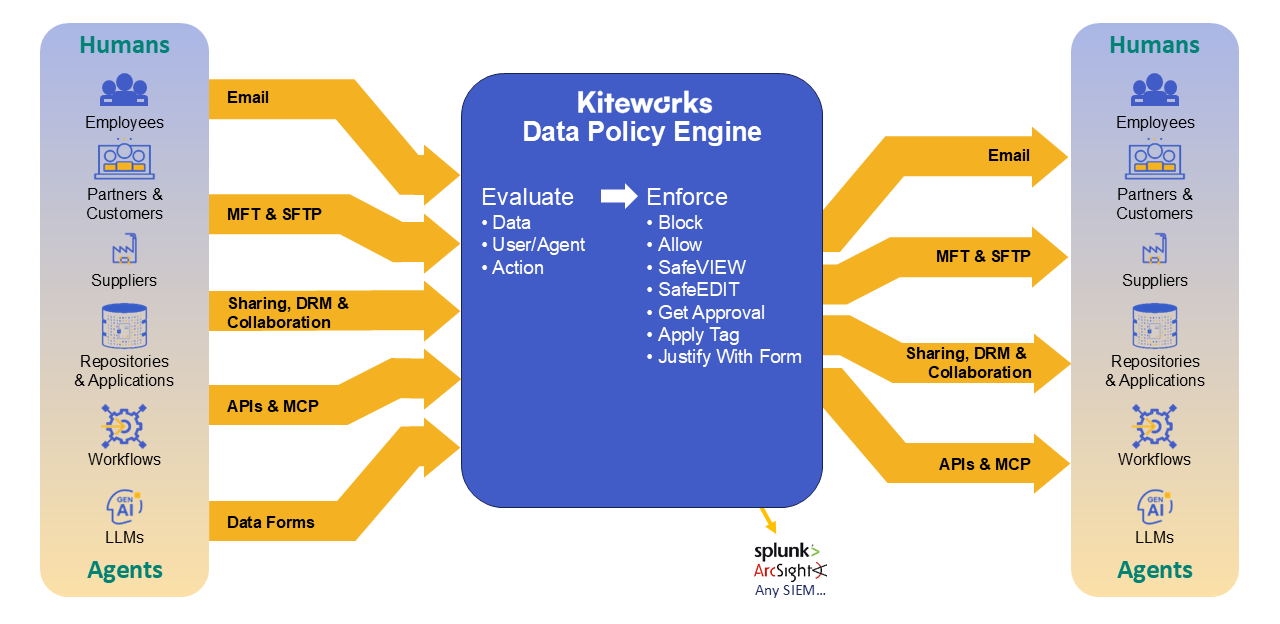
The Data Policy Engine is the enforcement layer of the Kiteworks secure data exchange platform. It ensures that every piece of sensitive data moving into, out of, or through your organization — whether accessed by an employee or an AI agent — follows the ABAC and RBAC rules you set, automatically and consistently, across every channel.

End the Policy Silos That Create Compliance Gaps and Audit Failures
Sensitive data flows across email, secure file sharing, managed file transfer, APIs, and data forms — and most organizations have no unified way to govern it. Policies exist in silos: one tool for email, another for file transfer, another for collaboration, none of them coordinated. The result is inconsistent enforcement, compliance gaps, and audit nightmares that leave security and compliance teams reacting instead of governing.
Unify Sensitive Data Governance Across Every Channel With One Control Plane
Every modern enterprise manages an application layer, a network layer, and an infrastructure layer — each with a control plane that governs behavior at scale. But sensitive data has historically had no control plane of its own. The Kiteworks platform changes that. It serves as the control plane for your organization’s sensitive data layer: a single platform through which all sensitive data exchanges flow, governed by consistent policy, protected by enterprise-grade security, and captured in a unified audit log. At the heart of that control plane is the Data Policy Engine.

Enforce Data Governance Automatically Across Every Channel With the Data Policy Engine
The Kiteworks Data Policy Engine draws on NIST Cybersecurity Framework principles to evaluate every sensitive data exchange across three factors simultaneously: what data is involved, who or what agent is taking the action, and what they are trying to do. That triangulation, known as attribute-based access control (ABAC), drives dynamic, real-time policy decisions for employees and AI agents alike, enforced automatically from a single control point. The rule set maps directly to frameworks including CMMC 2.0, HIPAA, GDPR, FedRAMP, and ITAR, and requires no manual intervention to enforce. Every action is logged in a comprehensive, immutable audit log that feeds directly into compliance reporting and SIEM integrations.

Accelerate Policy Deployment With Pre-Built Templates and IF-THEN Rule Logic
Define the attribute-based access control (ABAC) data policies as common-sense IF-THEN rules based on the data, user/agent, and action:
- IF the data has specific folder paths or data classifications (MIP sensitivity labels or Kiteworks tags), or email subject or body keywords.
- IF the user/agent has a specific domain, identity, profile, or real-time geolocation.
THEN set the directive based on the user/agent action:
- For data access action: Select blocking access, providing view-only access (SafeVIEW), possessionless editing access (SafeEDIT), requiring a justification form submission before access, or full access.
- For data sending or sharing action: Select blocking, requiring approval from designated managers before send/share, or allowing send/share.
- For data upload or attachment action: Select blocking, applying a specific Kiteworks tag, requiring a justification form submission before the action, or simply allowing the action.
Respond to Every Data Movement Instantly With Real-Time Policy Enforcement
-
Step 1 — Evaluate: As data moves across any Kiteworks channel, the DPE evaluates it in real time against your policy conditions — reading data attributes, identifying the actor (employee or AI agent), and determining the action requested.
-
Step 2 — Enforce: The matching directive fires automatically. No human intervention. Uniform enforcement across all channels and all actor types.


Govern Every User and Every Asset With Granular Role-Based Access Controls (RBAC)
Kiteworks least-privilege roles define what each class of user can do, such as file types they can upload, whether they can send email and with what forwarding and expiration options, which clients and plugins they can use, and whether they can create folders or invite other users. Administrative duties are separated across distinct roles to enable compliant management of privileges. At the folder level, granular access roles range from view-only through full management — with owners able to delegate day-to-day administration to managers. Time-based controls let administrators set expiration on user accounts, folders, files, and shared links, automatically revoking access when it is no longer needed.
Enforce Compliance Automatically and Prove It With a Comprehensive, Unified Audit Log
The Data Policy Engine makes compliance operational, not just documentable. Instead of proving adherence after the fact, Kiteworks enforces it in real time at the point of data movement. Policy controls map directly to specific regulatory requirements, automated enforcement eliminates human error and policy drift, and the unified audit log simplifies evidence collection for assessments and audits.
Sample of the regulatory frameworks supported:
- CMMC 2.0
- HIPAA / HITECH
- GDPR / NIS 2
- FedRAMP Moderate Authorized and FedRAMP High In Process
- ITAR / EAR
- SOC 2 Type II
- ISO 27001, 27017, 27018


Get More Than Policy Enforcement With a Complete Secure Data Exchange Platform
- The only platform that consolidates email, secure file sharing, MFT, SFTP, APIs, and data forms under a single policy framework and unified audit log — for both employees and AI agents.
- FedRAMP Moderate Authorized and FedRAMP High In Process — among the most rigorously security-validated platforms available for organizations with the most demanding compliance requirements.
- Hardened, single-tenant deployment options that give organizations with strict data isolation requirements full control over their environment, with no shared infrastructure.
- The CISO Dashboard provides real-time visibility into all sensitive data activity across every channel — who sent what to whom, when, and where — with drill-down reporting and direct SIEM integration.
Frequently Asked Questions
Policy silos refer to the fragmented approach of having separate policies for different tools like email, file transfer, and collaboration without coordination. This leads to inconsistent enforcement, compliance gaps, and audit failures, leaving security and compliance teams in a reactive mode rather than a governing one.
The Kiteworks platform acts as a control plane for sensitive data, allowing all exchanges to flow through a single platform. It enforces consistent policy, provides enterprise-grade security, and maintains a unified audit log, ensuring comprehensive governance across every channel.
The Data Policy Engine (DPE) is at the core of the Kiteworks platform, evaluating data movement in real time against policy conditions and enforcing directives automatically. It maps controls to regulatory requirements, eliminates human error, and simplifies evidence collection with a unified audit log for compliance assessments.
Beyond policy enforcement, Kiteworks provides a complete secure data exchange platform consolidating email, file sharing, MFT, SFTP, APIs, and data forms under one framework. It offers FedRAMP authorization, hardened single-tenant deployments, and a CISO Dashboard for real-time visibility and reporting on sensitive data activity.
FEATURED RESOURCES

Kiteworks Data Policy Engine: Automated Protection That Adapts to How You Work